From zero-day C2 detection to dark-web intelligence, Threatactix delivers analyst-grade cybersecurity services backed by real attacker infrastructure data.
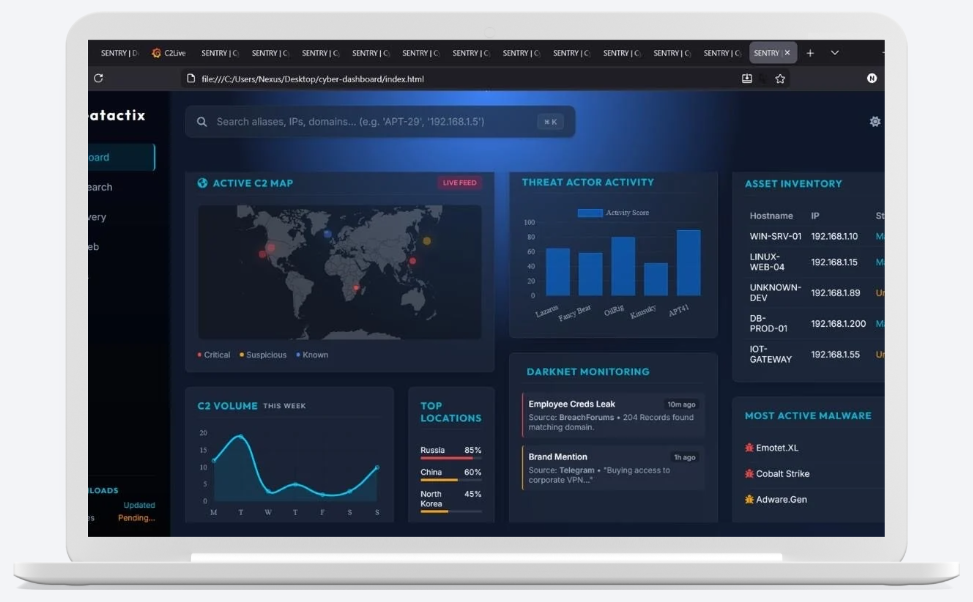

Identify attacker infrastructure before it becomes active

Real-time attacker insights

Proactive detection of hidden threats

Early detection before encryption begins
Discover & fix exposed digital assets
Validate your defenses using real attacker techniques

Track underground activity, leaks & threats

Hands-on interactive cybersecurity training
Continuous monitoring across attack surface, dark web, and global infrastructure.
Faster investigations, automated enrichment, and ready-to-use hypotheses.
Pre-ransomware signals, emerging malware infra, phishing prep activity.
Activate intelligence, automate hunting, and detect threats faster.