Successful Threat Hunting Village for Ransomware Theme Execution
The Seaside Security Conference Goa Feb-2025 featured a dedicated Threat Hunting Village, where cybersecurity professionals, researchers, and enthusiasts collaborated to analyze ransomware-themed execution techniques. Hosted and Designed by Threatactix and Seasides Team, this interactive experience provided attendees with real-world insights into ransomware operations, execution chains, and hunting methodologies.
Stage 1: Initial Compromise – Staging from a Word Document Macro
- Delivery Mechanism: A malicious Word document is sent to the victim via email as part of a phishing campaign. The email subject is tailored to the victim’s interests (e.g., “Invoice Due—Urgent Action Required”).
- The document includes a convincing message prompting the user to enable macros to “view the content properly.”
- Macro Execution: The malicious macro runs a VBA script once macros are enabled.
- The script: Downloads an additional payload (the ransomware executable) from a remote server or extracts it from an encoded portion of the document.
- Places the payload in a temporary directory (%TEMP% or %APPDATA%) for execution.
- Persistence Setup: The macro creates a registry key or schedules a task to ensure the ransomware runs on system reboot.
- Reconnaissance and Staging: The ransomware payload identifies critical directories and file types (e.g., .docx, .xlsx, .pdf, .jpg).
- It generates a unique encryption key for the session and sends it to the command-and-control (C2) server.
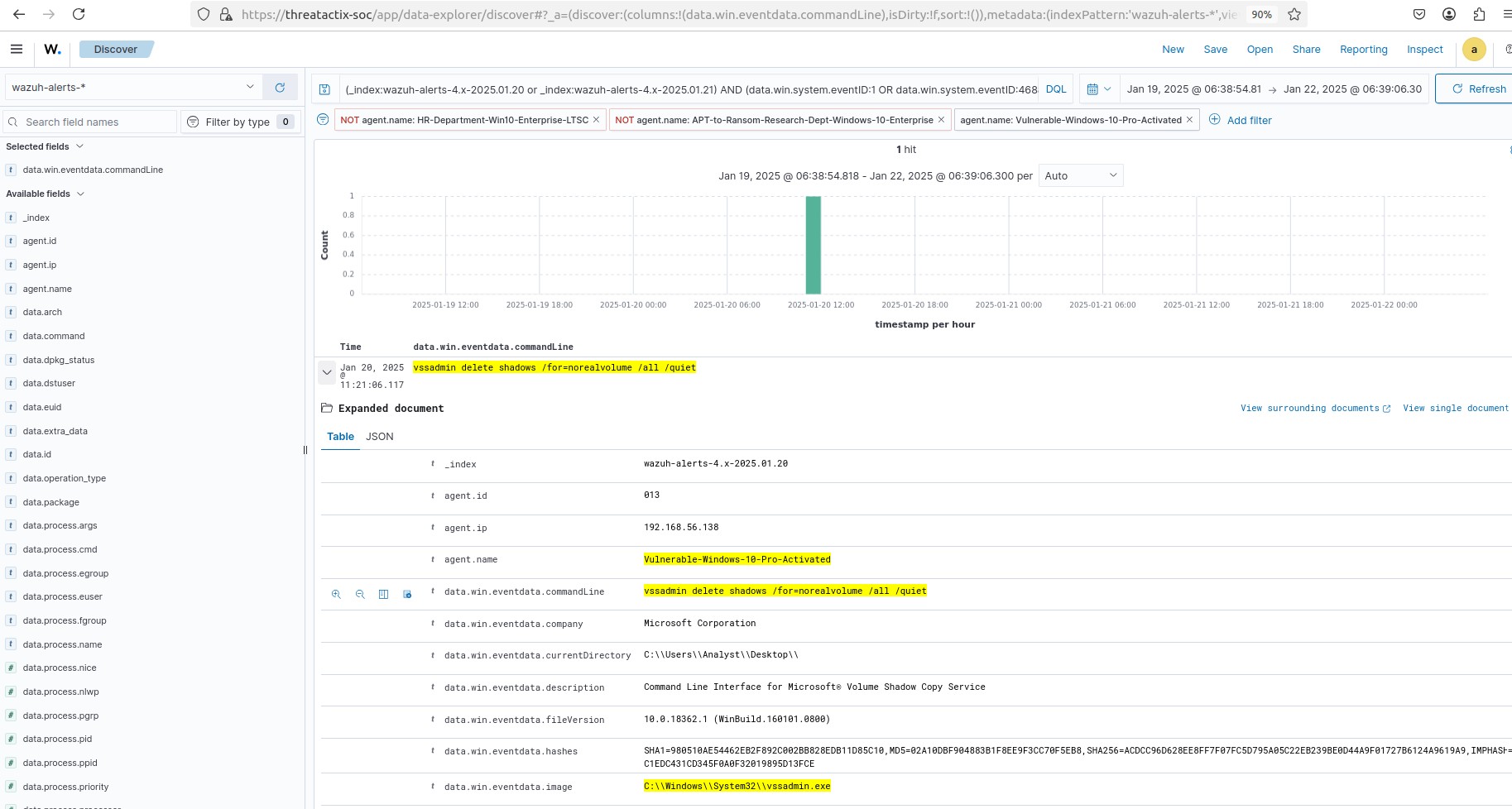
Stage 2: Deleting Volume Shadow Copies
- Execution of Commands: The ransomware executes commands to disable or delete Windows Volume Shadow Copies, preventing file recovery. For example:
- vssadmin delete shadows /all /quiet
- wmic shadowcopy delete
- System Hardening: It disables Windows Recovery options and clears system logs to prevent forensic analysis.
- wevtutil cl System
- wevtutil cl Security
Stage 3: File Encryption
- Encryption Preparation: The ransomware scans the system for predefined file types/extensions to encrypt.
- It skips critical system files to avoid breaking the system entirely, ensuring the victim can still interact with the ransom note.
- Simulating Document Encryption: The ransomware simulator encrypts documents dropped in a new folder (e.g., %USERPROFILE%\Documents\Encrypted_Files).
- Embedded documents (pre-dropped by the simulator) are encrypted in place with a custom extension (e.g., .encrypted).
- Encryption Execution: A symmetric encryption algorithm (e.g., AES) is used to encrypt files.
- A unique identifier (victim ID) is generated and embedded within the encrypted files for ransom tracking.
Stage 4: Dropping the Ransom Note
- Ransom Note Creation: A ransom note (e.g., README_DECRYPT.txt) is created on the user’s desktop and in each encrypted directory.
- The note includes:
- A warning about encrypted files.
- Instructions to pay the ransom (e.g., Bitcoin wallet address).
- A link to a TOR-based payment site for decryption assistance.
- A timer warns the victim of data deletion if payment is not made.
- Behavior Simulation: The ransomware note might open automatically via Notepad or a web browser to ensure the victim sees it.
Logs availability in Wazuh for Threat Hunting and Respective Tactics observed from Malicious Code Execution
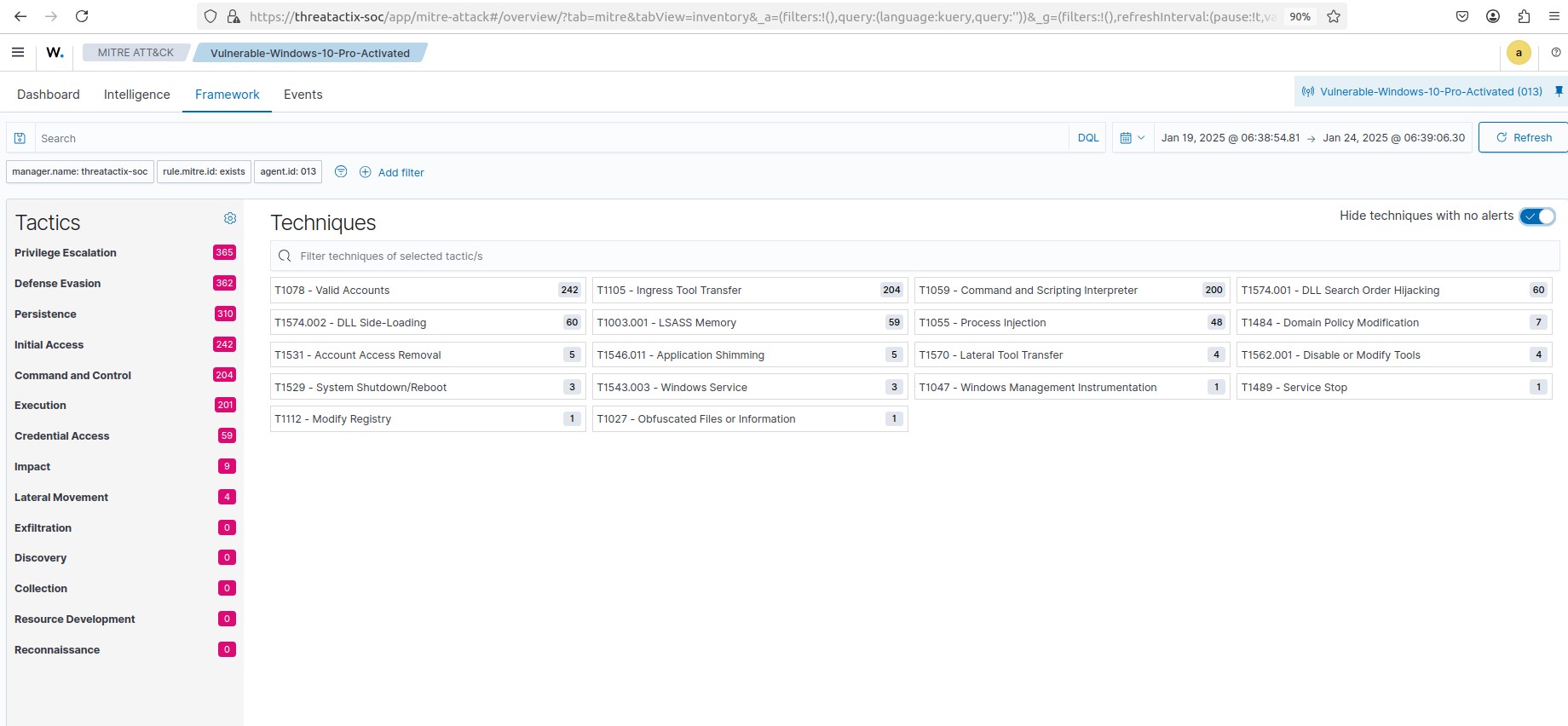
MITRE ATT&CK – Rules Detection – 647 Events
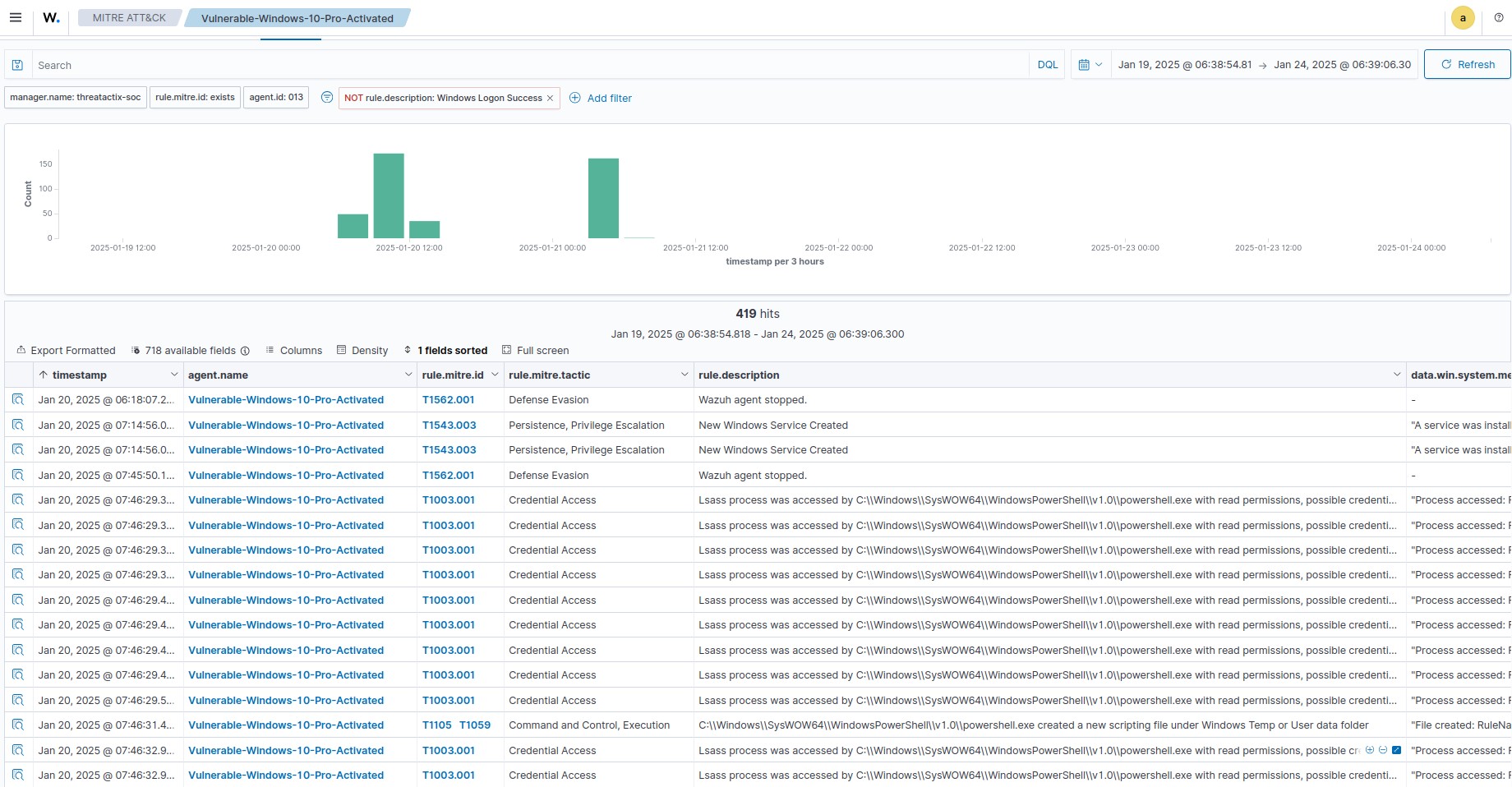
Threat Hunting Rules Detection – 34995 Events
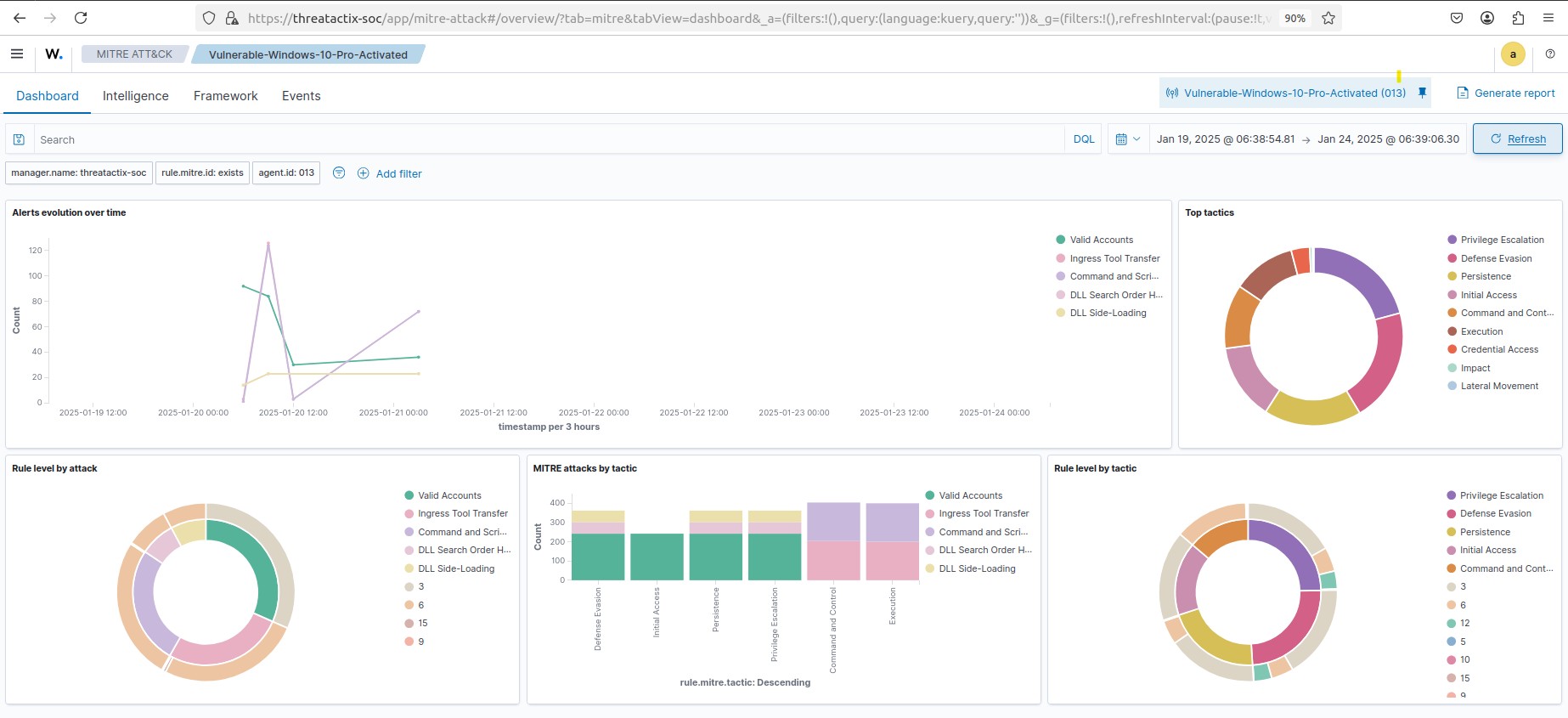
Wazuh Discover – Threat Hunting Queries – 34995 Events
Threat Hunting Queries and Detections
1. T1486 – Data Encrypted for Impact
Hypothesis Statement :
Adversaries may encrypt data on target systems or on large numbers of systems in a network to interrupt availability to system and network resources. They can attempt to render stored data inaccessible by encrypting files or data on local and remote drives and withholding access to a decryption key. This may be done to extract monetary compensation from a victim in exchange for decryption or a decryption key (ransomware) or to render data permanently inaccessible in cases where the key is not saved or transmitted.
2. T1490 – Inhibit System Recovery
Hypothesis Statement :
Adversaries may delete or remove built-in data and turn off services designed to aid in the recovery of a corrupted system to prevent recovery. This may deny access to available backups and recovery options.
Some native Windows utilities have been used by adversaries to disable or delete system recovery features:
- vssadmin.exe can be used to delete all volume shadow copies on a system – vssadmin.exe delete shadows /all /quiet
- Windows Management Instrumentation can be used to delete volume shadow copies – wmic shadowcopy delete
- wbadmin.exe can be used to delete the Windows Backup Catalog – wbadmin.exe delete catalog -quiet
- bcdedit.exe can be used to disable automatic Windows recovery features by modifying boot configuration data – bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no
- REAgentC.exe can be used to disable Windows Recovery Environment (WinRE) repair/recovery options of an infected system
- diskshadow.exe can be used to delete all volume shadow copies on a system – diskshadow delete shadows all
3. T1204.002 – User Execution: Malicious File
Hypothesis Statement :
An adversary may rely upon a user opening a malicious file in order to gain execution. Users may be subjected to social engineering to get them to open a file that will lead to code execution. This user action will typically be observed as follow-on behavior from Spearphishing Attachment. Adversaries may use several types of files that require a user to execute them, including .doc, .pdf, .xls, .rtf, .scr, .exe, .lnk, .pif, .cpl, and .reg.
Adversaries may employ various forms of Masquerading and Obfuscated Files or Information to increase the likelihood that a user will open and successfully execute a malicious file. These methods may include using a familiar naming convention and/or password protecting the file and supplying instructions to a user on how to open it
4. T1562.001 – Impair Defenses: Disable or Modify Tools
Hypothesis Statement :
Adversaries may modify and/or disable security tools to avoid possible detection of their malware/tools and activities. This may take many forms, such as killing security software processes or services, modifying/deleting Registry keys or configuration files so that tools do not operate properly, or other methods to interfere with security tools scanning or reporting information. Adversaries may also disable updates to prevent the latest security patches from reaching tools on victim systems
- G0047 – Gamaredon Group – Gamaredon Group has delivered macros that can tamper with Microsoft Office security settings.
- S0477 – Goopy – Goopy can disable Microsoft Outlook’s security policies to disable macro warnings
5. T1003.001 – LSASS Memory
Hypothesis Statement :
An unauthorized process (powershell.exe OR Other) running with NT AUTHORITY\SYSTEM privileges attempted to access lsass.exe, indicating a possible Credential Dumping (MITRE ATT&CK T1003) technique. This may be an attempt to extract password hashes, plaintext credentials, or Kerberos tickets from memory, which could lead to privilege escalation and lateral movement.
6. 1484 – Special privileges assigned to new logon.
Hypothesis Statement :
A threat actor has gained unauthorized access to a system using administrator-equivalent privileges, potentially leading to privilege escalation or lateral movement within the network. The goal is to identify, analyze, and mitigate any malicious activities originating from IP 192.168.56.138.
7. T1105 – Executable file dropped in folder commonly used by malware
Hypothesis Statement :
An adversary has dropped an executable file in a folder commonly used by malware, potentially indicating malicious activity.
8. T1059 – Command and Scripting Interpreter
Hypothesis Statement :
An adversary has leveraged a command-line or scripting interpreter (such as PowerShell, Bash, or Python) to execute potentially malicious commands or scripts on a compromised system.
9. T1574.001 – DLL Search Order Hijacking
Hypothesis Statement :
An attacker may have exploited DLL Search Order Hijacking (MITRE ATT&CK T1574.001) by placing a malicious UpdateAgent.dll in a location where a privileged process (svchost.exe) loads it, potentially achieving persistence, privilege escalation, and defense evasion.
10. T1055 – Process Injection
Hypothesis Statement :
A potentially malicious process (Procmon64.exe) located in the temporary directory (C:\Users\Analyst\AppData\Local\Temp\Procmon64.exe) accessed Explorer.exe, which could indicate process injection, masquerading, or reconnaissance activity. The investigation aims to determine whether this access was legitimate or part of an attack involving privilege escalation or defense evasion.
11. T1036 – Masquerading
Hypothesis Statement :
Adversaries may attempt to manipulate features of their artifacts to make them appear legitimate or benign to users and/or security tools. Masquerading occurs when the name or location of an object, legitimate or malicious, is manipulated or abused for the sake of evading defenses and observation. This may include manipulating file metadata, tricking users into misidentifying the file type, and giving legitimate task or service names.
Renaming abusable system utilities to evade security monitoring is also a form of Masquerading.
Conclusion
The Threat Hunting Village for Ransomware Theme Execution was a major success, equipping participants with practical threat-hunting skills and a deeper understanding of ransomware operations. By analyzing real-world attacks, attendees gained actionable intelligence to enhance their cybersecurity posture.